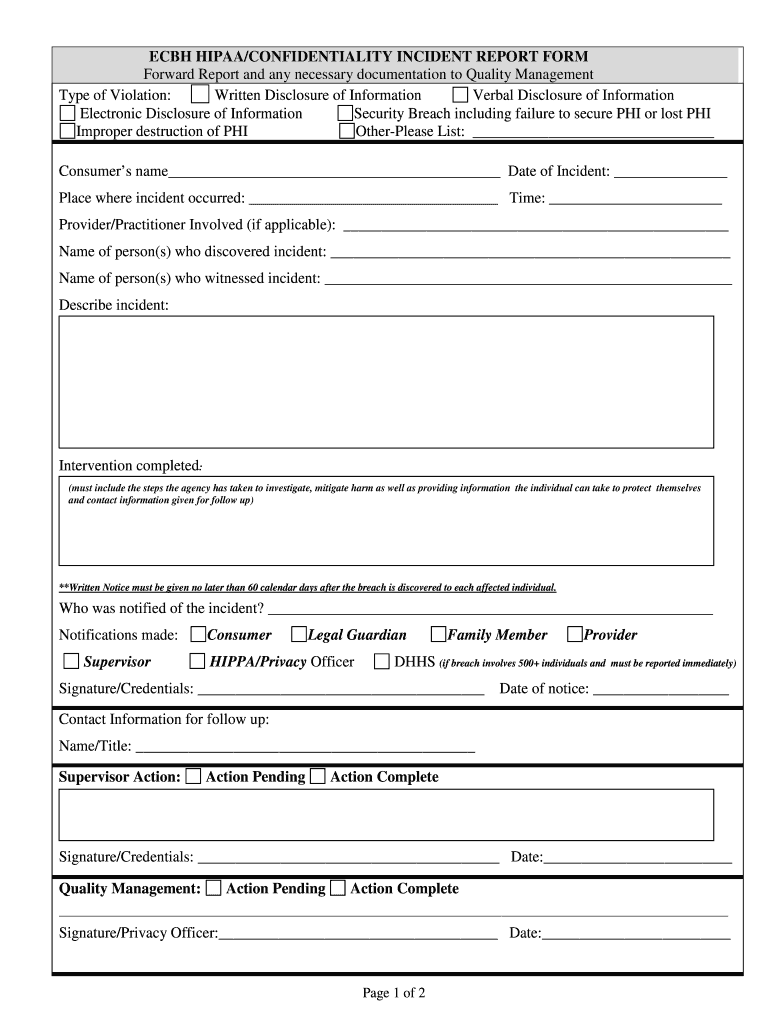
Understanding the HIPAA Incident Report Form
The HIPAA incident report form is a vital document used to report potential violations regarding the disclosure and security of Protected Health Information (PHI). This form serves as a structured approach for organizations in the healthcare sector to document incidents, assess their impacts, and implement corrective measures.
Purpose of the HIPAA Incident Report Form
The primary function of this form is to ensure that any violation or suspected violation of HIPAA regulations is properly documented. This documentation helps in:
- Identification: Recognizing instances where PHI may have been compromised.
- Monitoring: Keeping track of recurring issues that could indicate systematic problems within organizational policies or practices.
- Remediation: Offering a basis for corrective measures to prevent future violations.
Key Components of the HIPAA Incident Report Form
Each HIPAA incident report form typically includes several essential sections that guide the user in documenting details accurately.
- Incident Description: Provides a detailed account of the incident, including what occurred and how it happened.
- Individuals Involved: Identifies those who were present during the incident or whose PHI may have been compromised.
- Date and Time: Records when the incident occurred, which is crucial for timelines and follow-up actions.
- Response Actions Taken: Details what immediate steps were taken to mitigate the impact of the incident.
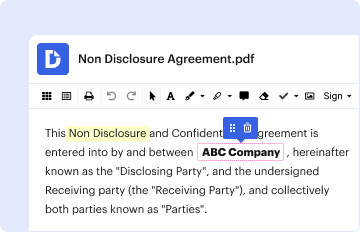
Steps for Completing the HIPAA Incident Report Form
Completing the form involves several systematic steps:
-
Documenting the Incident:
- Fill in the date and time of the incident.
- Provide a thorough description of the incident.
-
Identifying Affected Individuals:
- List all parties whose PHI was affected.
- Assign roles for those involved to clarify responsibilities.
-
Reporting Procedures:
- Indicate who has been informed about the incident.
- Note if the incident has been escalated to supervisory or compliance officers.
-
Corrective Actions:
- Describe any actions taken immediately following the incident.
- Outline preventive measures implemented to avoid future occurrences.
-
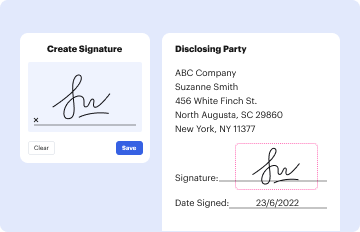
Review and Sign-off:
- Have the relevant personnel review the report for accuracy.
- Obtain signatures from responsible parties to finalize the report.
Examples of Unintentional HIPAA Violations
Understanding common unintentional violations can provide context for completing the report. Examples include:
- Accidental Disclosure: Sending an email containing PHI to the wrong recipient.
- Lost Devices: Misplacing a mobile device that contains unencrypted patient information.
- Accessing Records: An employee inadvertently viewing a patient’s medical records without authorization.
Legal Requirements Surrounding the HIPAA Incident Report Form
Several legal obligations exist regarding the completion and submission of this form:
- Timeliness: Organizations are required to report HIPAA incidents within a specified time frame to ensure prompt action.
- Notification: Affected individuals often must be notified when their PHI has been compromised, especially following a breach incident.
- Retention of Records: Completed HIPAA incident reports should be securely stored as per regulatory requirements to ensure compliance during potential audits or investigations.
Implications for Non-Compliance
Failing to properly document incidents or not addressing reported violations can lead to severe consequences:
- Fines and Penalties: Organizations may face significant financial penalties from regulatory bodies for non-compliance.
- Reputation Damage: Breaches of patient privacy can harm trust between healthcare providers and patients.
- Operational Challenges: Incidents not addressed may lead to systemic issues within the organization that can affect overall service delivery.
Conclusion on the Importance of the HIPAA Incident Report Form
The HIPAA incident report form is not merely a bureaucratic requirement but a crucial tool for safeguarding patient privacy and ensuring compliance with federal regulations. By understanding its components, procedures, and implications, organizations can foster a culture of accountability and continuous improvement in managing PHI security.