Whether you are already used to dealing with csv or handling this format the very first time, editing it should not feel like a challenge. Different formats may require specific applications to open and modify them effectively. Nevertheless, if you have to quickly work in formula in csv as a part of your usual process, it is advisable to find a document multitool that allows for all types of such operations without the need of additional effort.
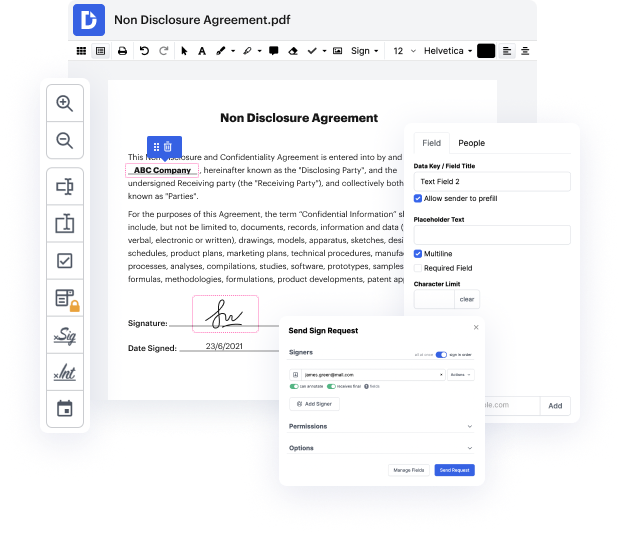
Try DocHub for efficient editing of csv and other file formats. Our platform provides effortless papers processing no matter how much or little prior experience you have. With all tools you have to work in any format, you will not need to jump between editing windows when working with each of your files. Effortlessly create, edit, annotate and share your documents to save time on minor editing tasks. You’ll just need to register a new DocHub account, and you can start your work instantly.
See an improvement in document management efficiency with DocHub’s straightforward feature set. Edit any file quickly and easily, irrespective of its format. Enjoy all the benefits that come from our platform’s simplicity and convenience.
Today's episode discusses functionality that can be used for phishing attacks, which can be found on websites that export data to CSV format. Excel, created by Microsoft, offers many built-in functions for accounting purposes. Formulas in Excel are initiated with the equality sign, allowing for calculations like finding the average of numbers from given cells. The program also allows for creating links to external websites or executing external programs using a functionality called DDE. Microsoft warns users about potential risks before executing potentially dangerous code through DDE.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



