Keeping pace with the fast-transforming work environment that has appeared since COVID remains a crucial concern for so many sectors. Many companies search for an available and easy-to-implement remedy that would be available for them 24/7. The key interest is based on addressing all document generation and approval procedures with minimum effort and time. DocHub offers powerful features and storage space integrations that will improve your every day document processes forever. You just need a free DocHub profile to access Word Tool - Tls.
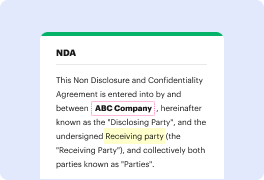
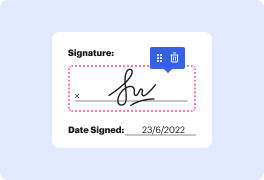
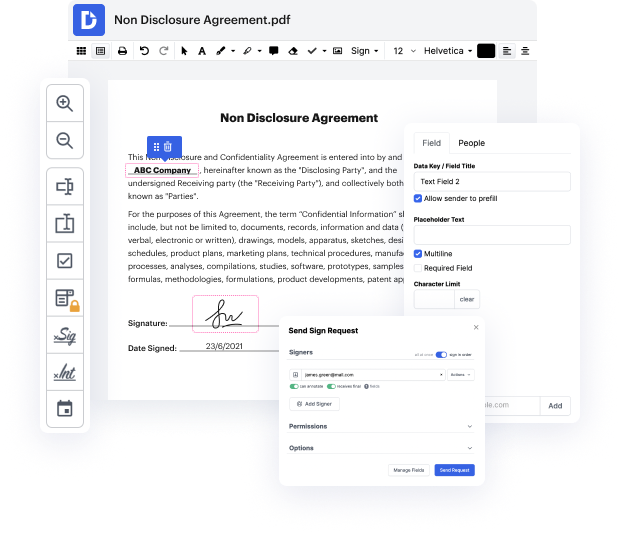
DocHub is an end-to-end editing and annotation solution that addresses all your document generation demands. Create documents from scratch, modify them, leave feedback, and swiftly gather signatures from teammates and clients. Forget about losing your files or fearing about safety - DocHub has industry-leading safety standards that protect your information.
Work on agreements and contracts anyplace, at any time. Get the most from Word Tool - Tls and increase your every day document administration, from document creation to approval and storage space.
This lesson covers how SSL and TLS use cryptographic tools like confidentiality, integrity, and authentication. It serves as a mini review of these concepts, emphasizing the importance of understanding how they fit together in the SSL/TLS world. SSL and TLS have three main purposes: confidentiality, integrity, and authentication, each provided by different cryptographic tools. Encryption ensures confidentiality, integrity prevents data modification, and authentication verifies the identity of the parties involved.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



