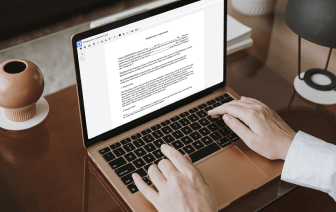
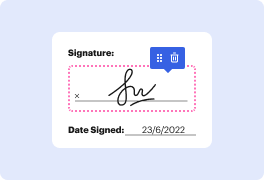
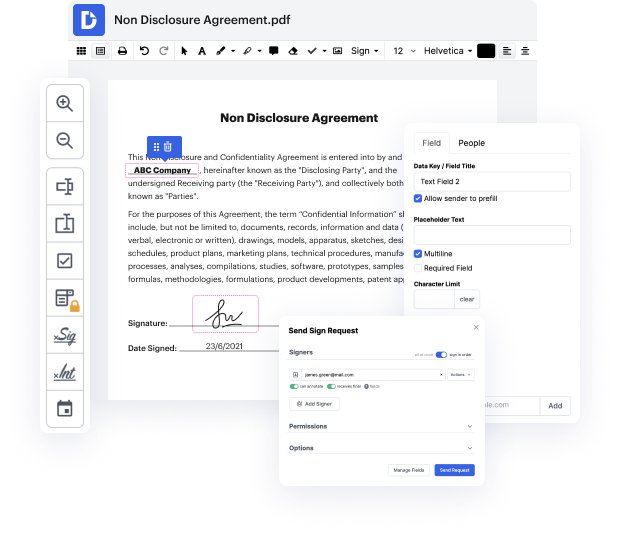
You no longer have to worry about how to wipe out PII in LOG. Our extensive solution guarantees easy and quick document management, allowing you to work on LOG documents in a few minutes instead of hours or days. Our platform includes all the features you need: merging, inserting fillable fields, approving forms legally, inserting signs, and much more. You don't need to install extra software or bother with costly programs demanding a powerful computer. With only two clicks in your browser, you can access everything you need.
Start now and handle all different types of files like a pro!
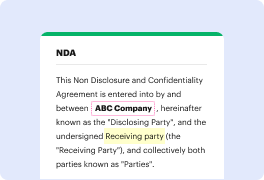
when youamp;#39;re talking about federal systems they have a bunch of controls that youamp;#39;re supposed to meet in order to protect the personally identifiable information starting from the top you have to your organization should have a policy and procedure you should have an authority to process personally identifiable information and normally what theyamp;#39;ll have is like a cpo or a privacy czar or privacy manager or some kind of authority thatamp;#39;s backed by law personally identifiable information processing purpose you need to have a purpose of every system thatamp;#39;s actually identifying personally identifiable information consent to actually get their personally identifiable information particularly for customers and things like subscribers or whatever also a privacy notice is something you probably have seen on many different websites especially on federal or state websites pt6 goes into system of records notice or assorn where if you have a searchable databas