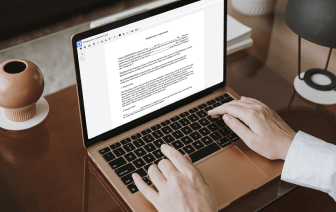
If you edit documents in various formats daily, the universality of your document tools matters a lot. If your instruments work with only a few of the popular formats, you might find yourself switching between software windows to void URL in ACL and handle other file formats. If you wish to get rid of the hassle of document editing, go for a solution that can effortlessly handle any format.
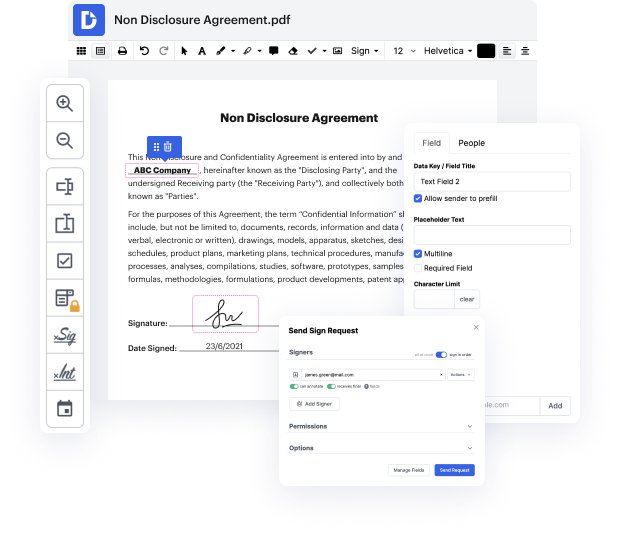
With DocHub, you do not need to focus on anything but actual document editing. You won’t have to juggle applications to work with various formats. It will help you revise your ACL as effortlessly as any other format. Create ACL documents, edit, and share them in one online editing solution that saves you time and boosts your productivity. All you have to do is sign up a free account at DocHub, which takes only a few minutes or so.
You won’t need to become an editing multitasker with DocHub. Its feature set is enough for speedy document editing, regardless of the format you need to revise. Begin with creating a free account and discover how straightforward document management can be having a tool designed particularly to meet your needs.
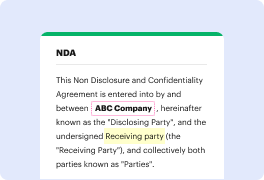
hello and this is sunny welcome back and Internet is a private network which is heavily protected by many different networking devices such as a router firewall proxy server DMZ honeynet IPs and IDs this diagram is an overly simplified version of the reality I try to pull these devices together in a reasonable order only for teaching and learning purpose today my topic is rotters access control list or ACL a [Music] router is used to connect networks together and is primary function is to deliver packets based on layer 3 IP address this is the most important function of a router I will have a separate video talking about the routers today I only focus on one of the routers of security features a CL AC L stands for access control list which is a setup to conquer the traffic in both directions incoming and outgoing a CL tells rodder to permit or deny traffic according to one or more of the following variables source IP address source subnet mask destination IP address destination subnet