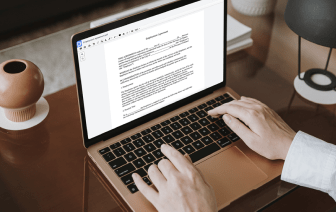
If you edit documents in different formats day-to-day, the universality of the document solution matters a lot. If your instruments work for only a few of the popular formats, you might find yourself switching between application windows to void print in Amigaguide and manage other document formats. If you want to take away the headache of document editing, go for a platform that can effortlessly manage any format.
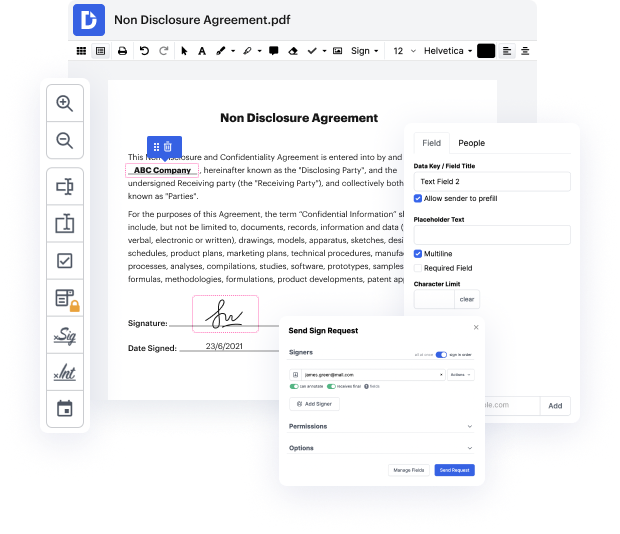
With DocHub, you do not need to focus on anything short of the actual document editing. You will not have to juggle applications to work with different formats. It will help you edit your Amigaguide as effortlessly as any other format. Create Amigaguide documents, edit, and share them in a single online editing platform that saves you time and boosts your efficiency. All you need to do is register a free account at DocHub, which takes only a few minutes or so.
You will not have to become an editing multitasker with DocHub. Its functionality is sufficient for fast document editing, regardless of the format you want to revise. Begin with registering a free account and discover how straightforward document management might be having a tool designed specifically for your needs.
welcome back everybody to another youtube video showcasing more of the pico ctf 2022 capture the flag were just getting started on some of the early beginner basic challenges and making our way through in the last video we just did honestly a wrought 13 caesar cipher kind of simple cryptography stuff and now we are continuing onward so hey lets hop onto the computer screen and have some more fun uh i am going to be cruising into this next challenge called its in the binary exploitation category its cve xxxxxx whatever um i gotta be honest theyre theyre youre not doing much binary exploitation in this challenge it says enter the cve or the what is that common vulnerability is an ex im im totally getting that acronym wrong but its a its a vulnerability its a flaw to weakness its a security issue and youll enter the flag as the correct flag format so passing that in just like that youll replace the numbers for a matching vulnerability based off of the first recorded remote