Document generation and approval are a central priority for each organization. Whether dealing with large bulks of documents or a particular agreement, you must stay at the top of your productivity. Choosing a perfect online platform that tackles your most typical file creation and approval obstacles could result in quite a lot of work. Numerous online platforms offer just a restricted list of editing and signature functions, some of which could possibly be valuable to manage jpg formatting. A solution that handles any formatting and task will be a outstanding option when picking application.
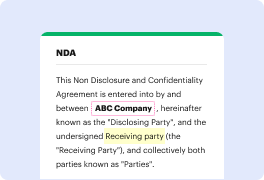
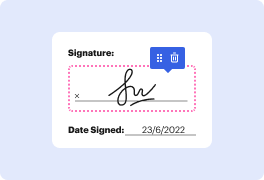
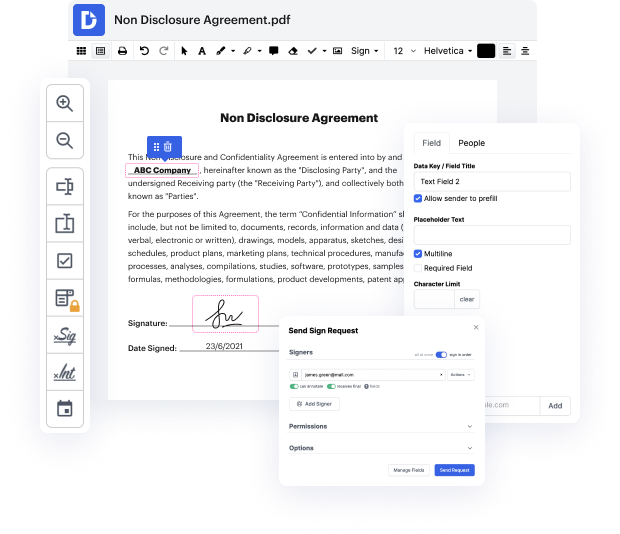
Get document management and creation to another level of simplicity and sophistication without choosing an difficult interface or pricey subscription plan. DocHub offers you tools and features to deal effectively with all of document types, including jpg, and carry out tasks of any complexity. Edit, arrange, that will create reusable fillable forms without effort. Get complete freedom and flexibility to void PII in jpg at any time and securely store all of your complete files within your user profile or one of many possible integrated cloud storage space platforms.
DocHub provides loss-free editing, signature collection, and jpg management on a professional level. You don’t have to go through tedious guides and invest countless hours figuring out the application. Make top-tier safe document editing a regular practice for your everyday workflows.
[Music] personally identifiable information what is pii pii is personally identifiable information that includes a persons name the names of family or friends addresses dates and places of birth social security numbers account numbers and even employee id numbers a personal data bdocHub occurs when pii is released to an unauthorized actor through email phishing attacks ransomware and even exploiting a victims digital footprints a digital footprint could be a potential piece of pii that exists on the internet as a result of a persons online activity easily harvested and then exploited by a threat actor cyber criminals can post ads on the dark web selling ones pii the identities are then bought by thieves to take part in tax fraud open fake accounts to apply for credit cards apply for work apply for a place to live and other exploitative crimes attackers can gather pii from anywhere including public forums and social media every type of organization businesses clinics and even school
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



