Whether you are already used to working with xhtml or handling this format the very first time, editing it should not seem like a challenge. Different formats might require specific apps to open and edit them properly. Yet, if you need to swiftly void cross in xhtml as a part of your typical process, it is advisable to find a document multitool that allows for all types of such operations without extra effort.
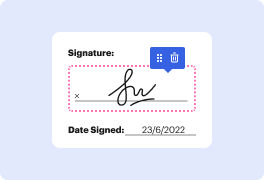
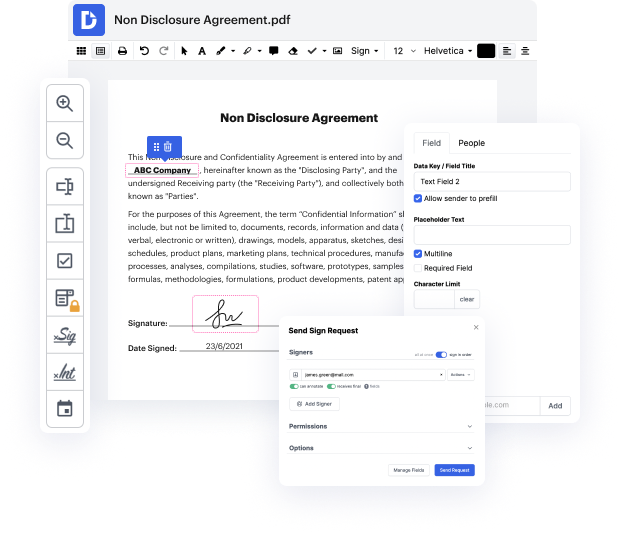
Try DocHub for streamlined editing of xhtml and also other file formats. Our platform provides easy document processing regardless of how much or little previous experience you have. With all instruments you need to work in any format, you will not need to jump between editing windows when working with every one of your documents. Effortlessly create, edit, annotate and share your documents to save time on minor editing tasks. You’ll just need to sign up a new DocHub account, and you can start your work right away.
See an improvement in document management efficiency with DocHub’s straightforward feature set. Edit any file quickly and easily, irrespective of its format. Enjoy all the advantages that come from our platform’s efficiency and convenience.
hello guys Welcome to our Channel today we are going to learn about cross-site scripting and its types this is an educational video for cyber security beginners and anybody who wants to learn what is cross-site scripting that is xxs cross-site scripting xss is a type of security vulnerability that allows an attacker to inject malicious code into a web page viewed by other users this can be done by exploiting a weakness in the way the website processes user input when a user visits a compromised web page the malicious code is executed in their browser giving the attacker the ability to steal sensitive information such as login credentials or perform other malicious actions such as redirecting the user to a phishing website there are two types of xss stored and reflected stored xss is when the malicious script is permanently stored on the website server and is served to every user who views the affected page this type of attack is more dangerous as it can potentially affect a large numb
and close it with a closing paragraph tag
(closing tags always proceed the element with a /).