
Searching for a specialized tool that deals with particular formats can be time-consuming. Regardless of the vast number of online editors available, not all of them support NEIS format, and definitely not all allow you to make adjustments to your files. To make matters worse, not all of them give you the security you need to protect your devices and paperwork. DocHub is a great solution to these challenges.
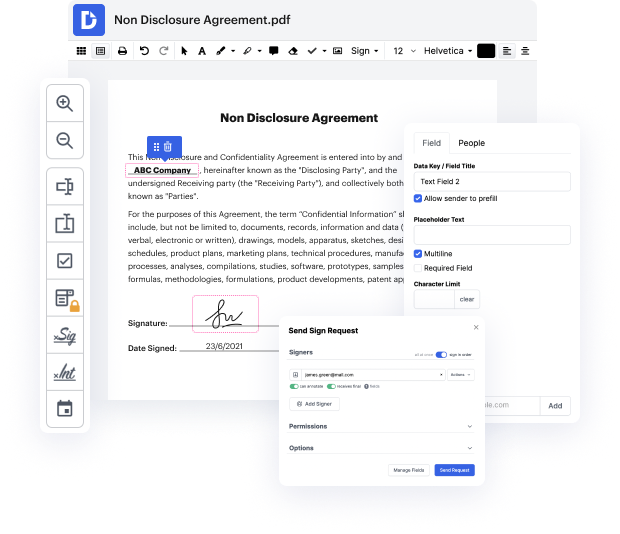
DocHub is a popular online solution that covers all of your document editing needs and safeguards your work with bank-level data protection. It works with various formats, such as NEIS, and helps you modify such paperwork easily and quickly with a rich and user-friendly interface. Our tool meets important security standards, such as GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps improving its compliance to guarantee the best user experience. With everything it provides, DocHub is the most reputable way to Void authentication in NEIS file and manage all of your individual and business paperwork, irrespective of how sensitive it is.
Once you complete all of your modifications, you can set a password on your updated NEIS to make sure that only authorized recipients can work with it. You can also save your document containing a detailed Audit Trail to see who applied what edits and at what time. Choose DocHub for any paperwork that you need to adjust safely and securely. Sign up now!
multi-factor authentication is implemented correctly it can be an extremely powerful and low-cost way to protect against the weakest link in the cyber security defense which is generally the user password it works by combining something you know like a password with something you have like a hard or soft it can be expanded to include other factors such as something you are like biometrics or somewhere you are like geolocation attacks on multi-factor authentication were once considered more of a proof of concept than an actual threat the thinking was as long as multi-factor authentication is enabled it doesnt really matter if an attacker gets a user password because it would still need access to the over recent years however more and more attacks have proven to not only be quite successful but quite common in the real world in this video well take a look at four of the most common multi-factor authentication attacks seen and increasingly being used in the wild along with ways to mit