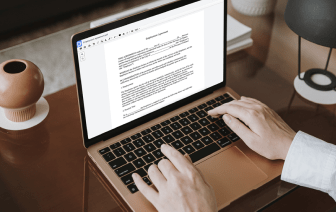
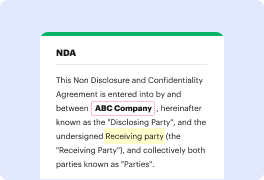
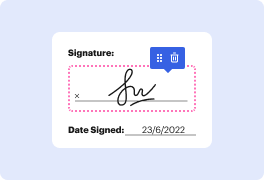
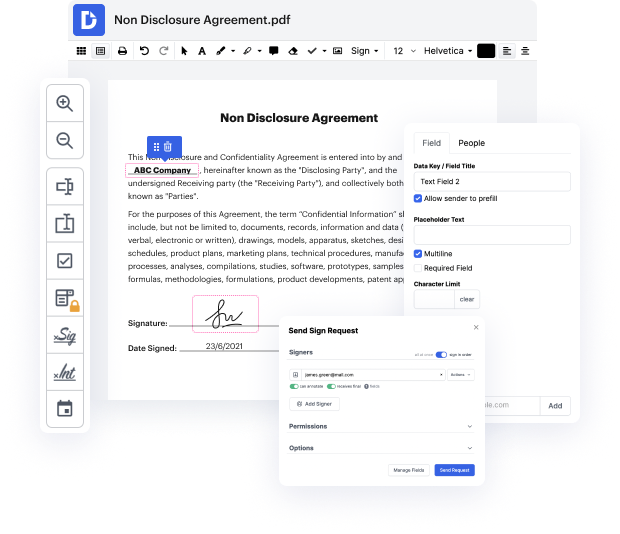
You no longer have to worry about how to vary authentication in ACL. Our powerful solution provides simple and fast document management, allowing you to work on ACL files in a couple of moments instead of hours or days. Our platform covers all the features you need: merging, adding fillable fields, signing forms legally, adding shapes, and so on. You don't need to install extra software or bother with costly applications demanding a powerful device. With only two clicks in your browser, you can access everything you need.
Start now and manage all various types of forms like a pro!
There are a few ways that we can control access to our buckets and the objects that we store within our S3 buckets, so in this lesson, Iamp;#39;m going to walk you through IAM policies, bucket policies, and access control lists. And then in the next couple of lessons, weamp;#39;ll do hands-on to see these in action as well. So firstly, we have policies created in the Identity and Access Management service. Now, these are identity-based policies, which means that they get associated with principles like users and roles. So with an IAM policy, weamp;#39;re directly applying the permissions that we want to assign to a principal, to that principal. Or we might be applying them to a group by attaching a policy to a group and then adding a user into the group. We can specify what actions are allowed on what AWS resources. So we can say that youamp;#39;re allowed to perform specific actions on a specific bucket, for example. So with IAM policies, these are atta