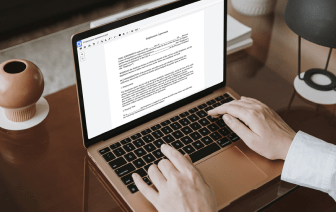

Unusual file formats within your daily document management and modifying operations can create instant confusion over how to edit them. You might need more than pre-installed computer software for efficient and quick document modifying. If you need to undo symbol in LOG or make any other simple change in your document, choose a document editor that has the features for you to deal with ease. To handle all of the formats, such as LOG, opting for an editor that works well with all kinds of files will be your best choice.
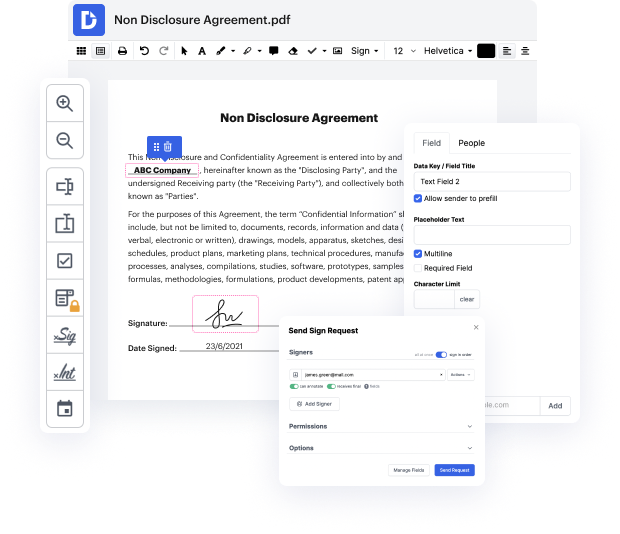
Try DocHub for efficient document management, irrespective of your document’s format. It offers powerful online editing instruments that simplify your document management operations. You can easily create, edit, annotate, and share any file, as all you need to access these features is an internet connection and an active DocHub profile. A single document solution is all you need. Do not waste time switching between different programs for different files.
Enjoy the efficiency of working with an instrument created specifically to simplify document processing. See how effortless it is to edit any document, even if it is the first time you have dealt with its format. Register a free account now and improve your entire working process.
now that we understand the different ways of logging lets talk about different recovery protocols the first one undo logging is one of the basic recovery protocols as we will see undo logging does not use right ahead logging that we covered earlier and it uses the force and steel mechanisms in terms of buffer pool management there are four types of lock records in an undo log start commits or abort of a transaction and finally an update record which states that transaction t wants to update data elements x and x previous value was v the idea behind undo logging is as follows we want to use the lock such that when we need to recover we will undo the effects of all the transactions that have not been committed on the other hand for all the transactions that have been committed we want to leave them alone in order to implement this behavior we need to establish a few rules regarding how we do logging and when to flush the dirty lock and data pages specifically there are two rules that w