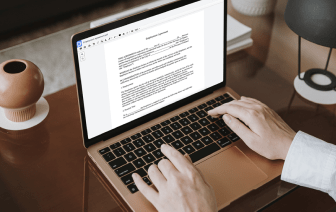
When your day-to-day work consists of plenty of document editing, you know that every document format needs its own approach and in some cases particular software. Handling a seemingly simple LOG file can sometimes grind the whole process to a stop, especially when you are trying to edit with inadequate software. To avoid this sort of troubles, find an editor that will cover your needs regardless of the file format and undo card in LOG without roadblocks.
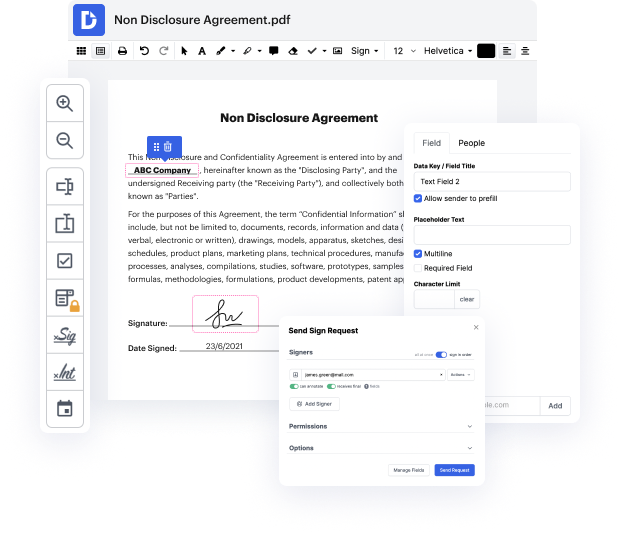
With DocHub, you will work with an editing multitool for virtually any situation or document type. Reduce the time you used to spend navigating your old software’s features and learn from our intuitive interface while you do the job. DocHub is a streamlined online editing platform that handles all your document processing needs for any file, such as LOG. Open it and go straight to productivity; no prior training or reading instructions is needed to reap the benefits DocHub brings to document management processing. Begin with taking a few moments to register your account now.
See upgrades within your document processing just after you open your DocHub account. Save your time on editing with our one solution that can help you become more efficient with any file format with which you need to work.
now that we understand the different ways of logging lets talk about different recovery protocols the first one undo logging is one of the basic recovery protocols as we will see undo logging does not use right ahead logging that we covered earlier and it uses the force and steel mechanisms in terms of buffer pool management there are four types of lock records in an undo log start commits or abort of a transaction and finally an update record which states that transaction t wants to update data elements x and x previous value was v the idea behind undo logging is as follows we want to use the lock such that when we need to recover we will undo the effects of all the transactions that have not been committed on the other hand for all the transactions that have been committed we want to leave them alone in order to implement this behavior we need to establish a few rules regarding how we do logging and when to flush the dirty lock and data pages specifically there are two rules that w