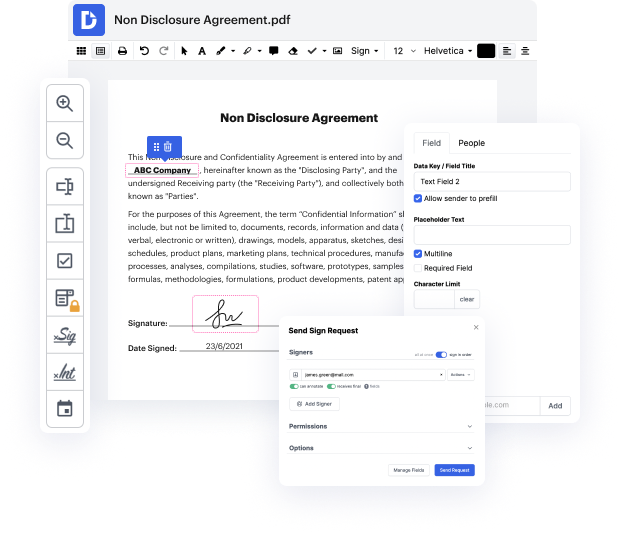
Browsing for a professional tool that deals with particular formats can be time-consuming. Despite the vast number of online editors available, not all of them are suitable for Xhtml format, and certainly not all allow you to make modifications to your files. To make matters worse, not all of them give you the security you need to protect your devices and documentation. DocHub is a great solution to these challenges.
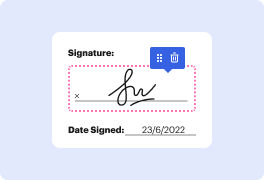
DocHub is a well-known online solution that covers all of your document editing requirements and safeguards your work with enterprise-level data protection. It works with different formats, such as Xhtml, and enables you to edit such paperwork easily and quickly with a rich and intuitive interface. Our tool meets essential security standards, such as GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps improving its compliance to guarantee the best user experience. With everything it offers, DocHub is the most reliable way to Tweak signature in Xhtml file and manage all of your individual and business documentation, irrespective of how sensitive it is.
After you complete all of your alterations, you can set a password on your edited Xhtml to ensure that only authorized recipients can open it. You can also save your paperwork with a detailed Audit Trail to find out who applied what edits and at what time. Select DocHub for any documentation that you need to adjust safely and securely. Subscribe now!
A cryptographic hash allows you to take any amount of data-- it can be a small bit of text, or it can be an entire book-- and you can represent that bit of data as a short string of text. We refer to this short string of hashed text as a message digest. A hash is not an encrypted version of the original text. Its really a one-way trip. Theres no way to recover the original text by simply looking at the hashed value. Its because of this unique characteristic that we commonly use hashes to store passwords. That way, we can compare a stored hash against another hash thats given to us later, but well still have no idea what the original password was from the user. We might also use hashes to confirm that a file that weve downloaded is identical to the original version of that file. And we use hashing during the creation of a digital signature that allows us to provide authentication, non-repudiation, and integrity to a particular document. A fundamental characteristic of hashing algo