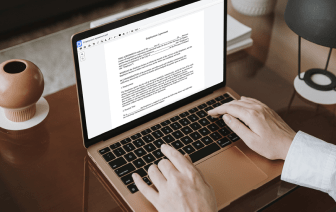
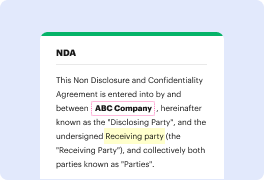
When you deal with different document types like warrant, you understand how important precision and attention to detail are. This document type has its specific format, so it is crucial to save it with the formatting intact. For this reason, working with such documents might be a challenge for traditional text editing software: one wrong action may mess up the format and take additional time to bring it back to normal.
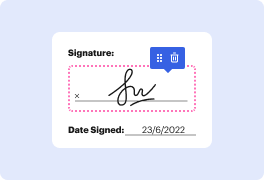
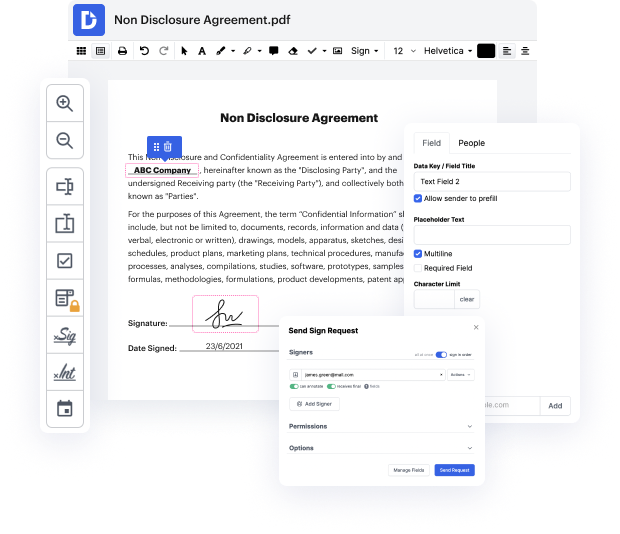
If you wish to tack number in warrant without any confusion, DocHub is a perfect tool for this kind of tasks. Our online editing platform simplifies the process for any action you might need to do with warrant. The streamlined interface is suitable for any user, whether that individual is used to working with this kind of software or has only opened it the very first time. Access all editing tools you require easily and save your time on everyday editing activities. You just need a DocHub profile.
See how effortless papers editing can be regardless of the document type on your hands. Access all top-notch editing features and enjoy streamlining your work on documents. Register your free account now and see immediate improvements in your editing experience.
Cellphone tracking and seizure have become essential for law enforcement, with the use of stingrays as popular means. Stingrays mimic cell towers to intercept phones for location tracking and eavesdropping without any warning. Concerns about privacy and abuse have led to the development of advanced handheld cell phone locators for legal and swift use by military, government, and law enforcement agencies, as well as security teams, private investigators, and correction officers.