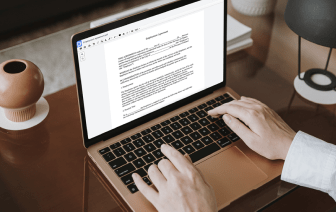
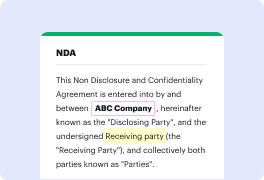
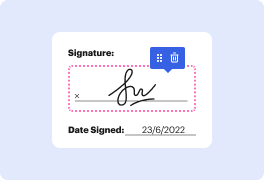
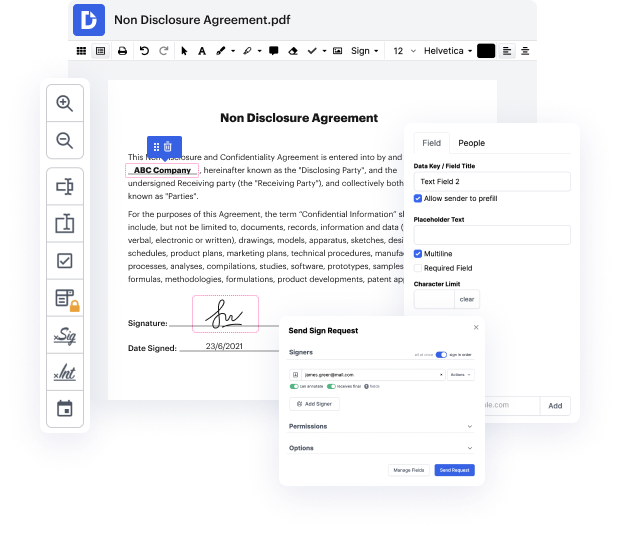
DocHub makes it quick and straightforward to strike password in RPT. No need to instal any extra application – simply upload your RPT to your account, use the easy drag-and-drop user interface, and quickly make edits. You can even work on your PC or mobile device to adjust your document online from any place. That's not all; DocHub is more than just an editor. It's an all-in-one document management solution with form constructing, eSignature features, and the ability to let others complete and sign documents.
Each file you upload you can find in your Documents folder. Create folders and organize records for easier search and access. Additionally, DocHub ensures the security of all its users' data by complying with strict protection standards.
hi guys welcome to my YouTube channel cyber security Ranger in my previous video I demonstrated how the passwords can be captured using um the error cap today Iamp;#39;m going to demonstrate that how we can use social engineering along with cloning a web page and then capture the usernames and passwords so the idea here is also to create awareness how easy it is to clone a website and then the emails that you receive in your uh you know inbox saying that click on the link and then it redirects you to a website which probably could be the website meant to capture your username and password so uh you know we should be avoiding that now the tool that Iamp;#39;m using for this particular demonstration is called the SCT toolkit social engineering toolkit so itamp;#39;s available in Cali you donamp;#39;t need to it just write SCT toolkit and then there you go itamp;#39;s pretty easy to use sat toolkit you donamp;#39;t need any commands so you just have to select the options from the me