Document generation and approval certainly are a core priority of each firm. Whether handling sizeable bulks of files or a certain contract, you need to stay at the top of your productiveness. Choosing a excellent online platform that tackles your most frequentl document generation and approval obstacles could result in quite a lot of work. Numerous online platforms offer you just a limited list of editing and eSignature functions, some of which might be useful to deal with csv formatting. A platform that handles any formatting and task might be a superior option when picking software.
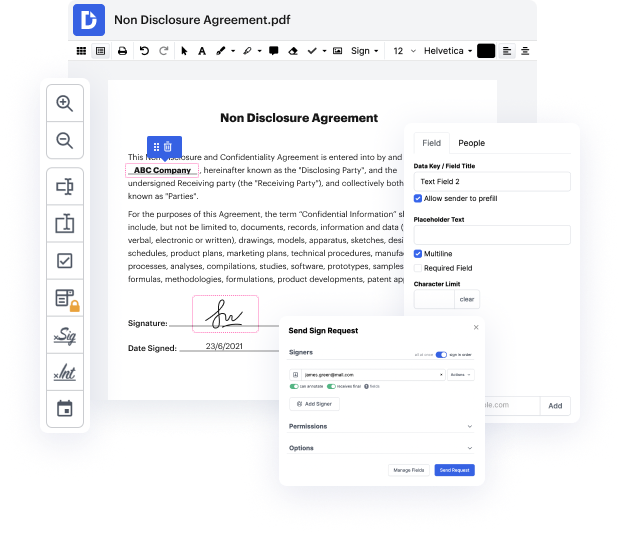
Take document administration and generation to a different level of simplicity and excellence without picking an awkward program interface or pricey subscription options. DocHub provides you with instruments and features to deal efficiently with all of document types, including csv, and perform tasks of any complexity. Change, arrange, that will create reusable fillable forms without effort. Get total freedom and flexibility to strike out side in csv at any time and securely store all of your complete documents in your profile or one of many possible integrated cloud storage platforms.
DocHub offers loss-free editing, signature collection, and csv administration on the expert level. You do not have to go through tedious tutorials and invest countless hours finding out the software. Make top-tier safe document editing a typical practice for your day-to-day workflows.
welcome to the ronio and duron podcast show im duron and im raniel in todays episode well be exploring csv injection and looking a little bit into how we can leverage different attacks to attack the client system its important to remember when we talk about attacking clients that it varies from client to client and how the data is going to be displayed for example if i am attacking a client that reads a csv or json or yaml or any other file i need to recognize how that data is being used or displayed as the case may be if for example the data within the file is being used to run operating system commands or queries or application commands or queries then obviously my attacks have to since im attacking the client be addressed in that vein if however the client is something such as the microsoft office excel client or libreoffice or anything of that nature then my attack needs to be based on whatever that happens to be so first and foremost weve added in some new functionality an
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



