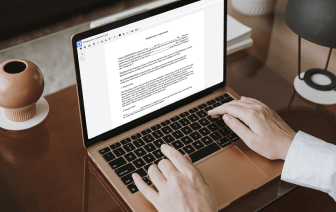
There are so many document editing solutions on the market, but only some are suitable for all file formats. Some tools are, on the other hand, versatile yet burdensome to work with. DocHub provides the answer to these hassles with its cloud-based editor. It offers powerful capabilities that allow you to accomplish your document management tasks efficiently. If you need to rapidly Strike identification in Xml, DocHub is the perfect choice for you!
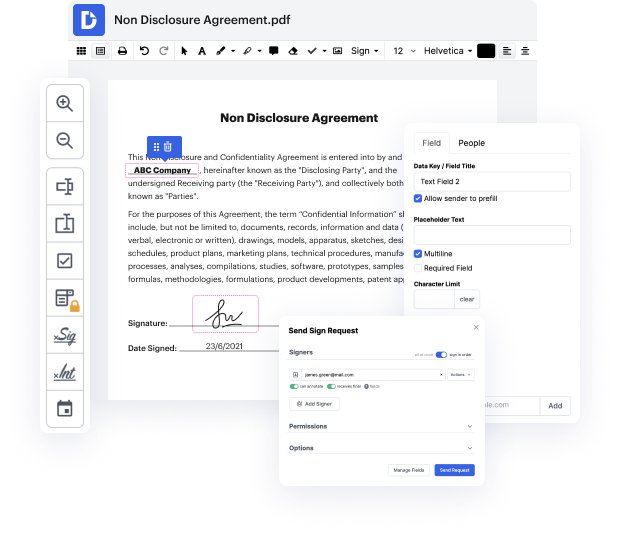
Our process is very easy: you upload your Xml file to our editor → it instantly transforms it to an editable format → you apply all essential adjustments and professionally update it. You only need a couple of moments to get your work done.
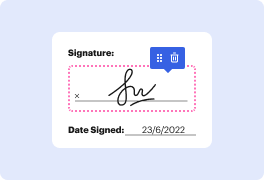
After all adjustments are applied, you can turn your paperwork into a reusable template. You just need to go to our editor’s left-side Menu and click on Actions → Convert to Template. You’ll locate your paperwork stored in a separate folder in your Dashboard, saving you time the next time you need the same form. Try DocHub today!
A code injection attack is when the attacker puts their own code into an existing data stream. This is often enabled because of bad programming with an application. An application shouldnt allow you to put your own code into a data stream. But, often, the code is not checked by the application, and attackers are able to exploit that vulnerability. Theres many different types of code that you can inject. You can inject HTML, or LDAP, or SQL code-- and any one of those may be able to manipulate or gather information from a machine, especially if you have control over the type of code that you would put into that data stream. One very common code injection type is a SQL injection. SQL stands for Structured Query Language-- or SQL. This is a very common relational database used on many websites. If you can circumvent the web front end, then you can gain access to the data thats in that database. Of course, the web front end should not allow these types of requests, but if the input is n