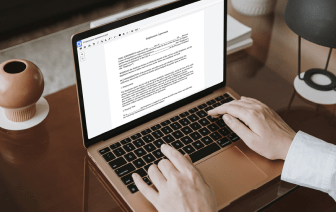

It is often hard to find a solution that may deal with all of your business demands or provides you with suitable instruments to control document creation and approval. Choosing an application or platform that combines essential document creation instruments that simplify any process you have in mind is critical. Although the most widely used formatting to work with is PDF, you require a comprehensive platform to manage any available formatting, including WPD.
DocHub ensures that all of your document creation requirements are covered. Edit, eSign, rotate and merge your pages in accordance with your requirements with a mouse click. Deal with all formats, including WPD, successfully and fast. Regardless of what formatting you begin dealing with, it is simple to convert it into a needed formatting. Save a great deal of time requesting or looking for the right document format.
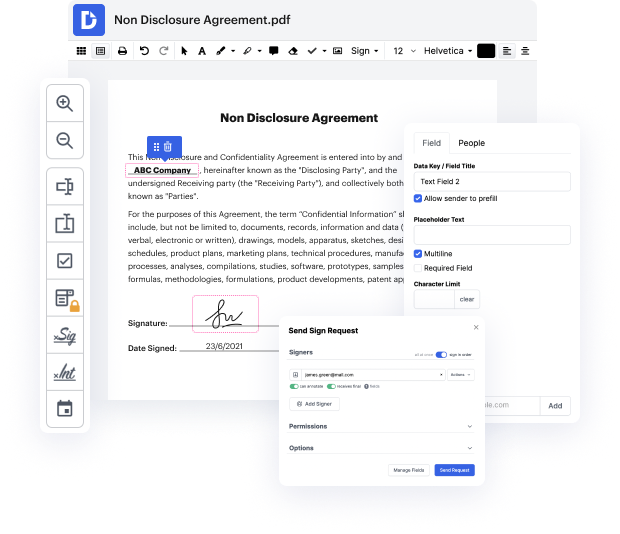
With DocHub, you do not require additional time to get familiar with our interface and editing procedure. DocHub is undoubtedly an easy-to-use and user-friendly software for anybody, even those without a tech background. Onboard your team and departments and enhance file administration for your business forever. strike email in WPD, create fillable forms, eSign your documents, and get things finished with DocHub.
Benefit from DocHub’s substantial feature list and rapidly work with any file in any formatting, such as WPD. Save your time cobbling together third-party software and stay with an all-in-one software to further improve your everyday procedures. Start your free of charge DocHub trial subscription right now.
[Laughter] hi there in this episode of our series on securing the remote workforce we want to take a deep dive into what every employee gets many times a day even more so now that theyre remote and which can pose a great threat on the security of an organization were talking about emails of course the risk from malicious emails must not be underestimated with over 90 of the attacks on organizations coming from this factor lets take a look at the latest in email-driven attacks type number one phishing this first type is quite familiar yet it has evolved greatly since the days of the email from the nigerian prince these days phishing emails involve very sophisticated social engineering techniques that are that are designed to exploit vulnerabilities both in systems and especially in human beings they include spoofing techniques that are designed to make the email look legitimate to the unsuspecting eye while there are different types of email phishing attacks the most common and