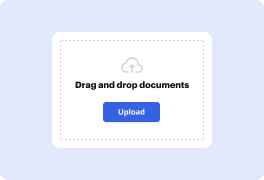
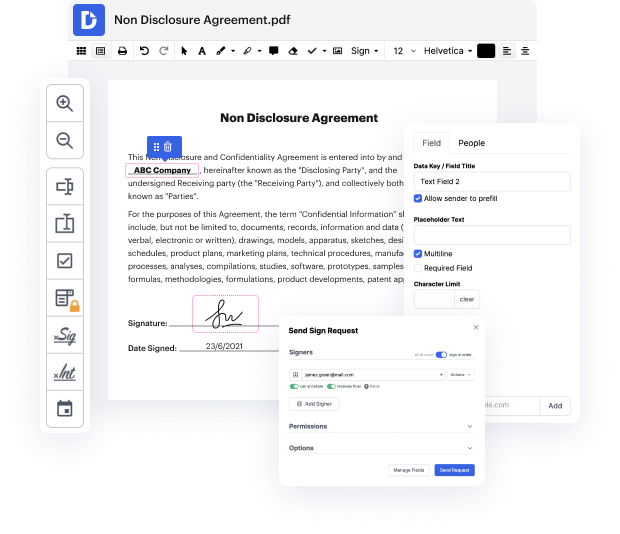
Searching for a specialized tool that handles particular formats can be time-consuming. Despite the vast number of online editors available, not all of them support Radix-64 format, and certainly not all enable you to make modifications to your files. To make things worse, not all of them provide the security you need to protect your devices and documentation. DocHub is a perfect solution to these challenges.
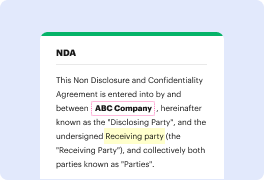
DocHub is a popular online solution that covers all of your document editing needs and safeguards your work with enterprise-level data protection. It works with different formats, such as Radix-64, and enables you to modify such paperwork quickly and easily with a rich and user-friendly interface. Our tool fulfills crucial security regulations, such as GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps improving its compliance to provide the best user experience. With everything it offers, DocHub is the most reputable way to Strike comment in Radix-64 file and manage all of your personal and business documentation, regardless of how sensitive it is.
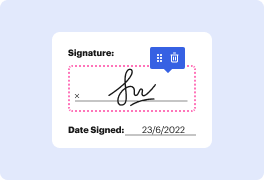
When you complete all of your alterations, you can set a password on your updated Radix-64 to make sure that only authorized recipients can work with it. You can also save your document with a detailed Audit Trail to check who made what changes and at what time. Select DocHub for any documentation that you need to adjust safely and securely. Subscribe now!
and today Ill be teaching you structured query language injection sqli [Music] so right in front of us we have open web application security project bricks so this is a vulnerable web application platform for us to load our SQL injection and payloads into the website so that we can gain access into different components of the database system and the database systems houses all the sensitive data records like usernames email addresses passwords whether the passwords are protected using hashes or not either way well learn about how to break into those passwords too and that is really scary because the first part is learning about how can we manually run our injection payloads into the site the second part is we can identify vulnerable parameters very very quickly and be able to pull out lots of information easily from a highly automated SQL injection tool and this is frightening because it speeds up the whole process of penetration testing into any website any web application platform
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



