Document generation and approval are a key focus of every firm. Whether dealing with sizeable bulks of documents or a specific agreement, you need to remain at the top of your productiveness. Choosing a perfect online platform that tackles your most common file creation and approval problems might result in a lot of work. Numerous online platforms offer you merely a limited list of editing and signature features, some of which may be useful to manage rtf formatting. A platform that handles any formatting and task will be a superior choice when selecting program.
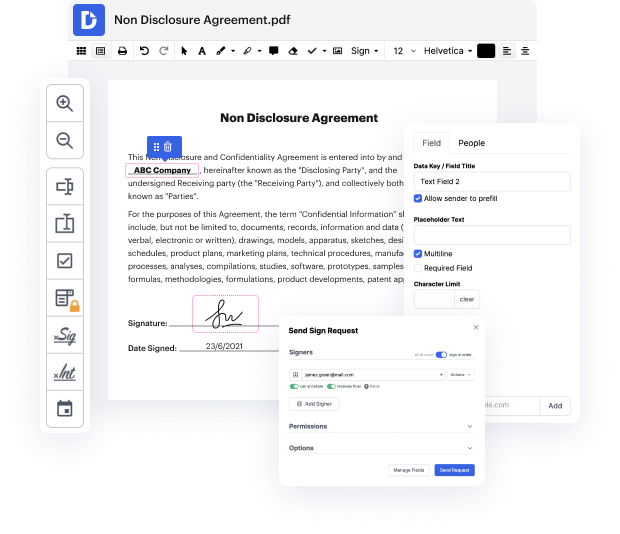
Take document management and creation to another level of simplicity and sophistication without opting for an difficult interface or costly subscription options. DocHub offers you instruments and features to deal successfully with all of document types, including rtf, and execute tasks of any complexity. Modify, organize, and produce reusable fillable forms without effort. Get complete freedom and flexibility to strike code in rtf anytime and safely store all your complete files in your account or one of many possible incorporated cloud storage platforms.
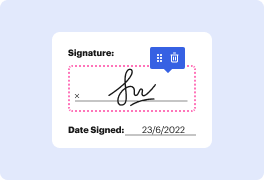
DocHub provides loss-free editing, eSignaturel collection, and rtf management on a expert levels. You don’t need to go through tiresome tutorials and invest a lot of time finding out the software. Make top-tier safe document editing a standard process for the daily workflows.
Heres a word document that someone sent me through email. We all know its not a good idea to blindly open files that someone sent you on the Internet. But, I am just going to download it, Im not even thinking of opening it, I am just downloading it to my computer. Okay, the file is downloaded and I now go to the location where this file is downloaded, and -- WHAT WAS THAT?? I got a message saying that I was hacked and it opened up the rick roll youtube video automatically. Now, I am re-stating this - I did not open the file, I just downloaded it and browsed to its location in File explorer with the preview pane. So I was only previewing the file! And that was enough for the hacker to hack me. He could even get a reverse shell to my computer and do literally anything on it. This is the recently discovered follina exploit which is assigned as CVE-2022-30190. In this video, I will show you how this exploit was discovered, how it works, and how to protect you
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



