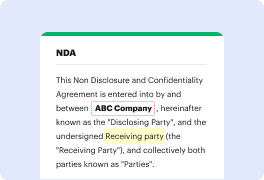
Unusual file formats in your everyday document management and modifying processes can create instant confusion over how to modify them. You might need more than pre-installed computer software for efficient and quick document modifying. If you need to strike account in Radix-64 or make any other simple change in your document, choose a document editor that has the features for you to deal with ease. To handle all of the formats, such as Radix-64, opting for an editor that works well with all types of files will be your best choice.
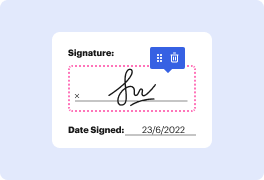
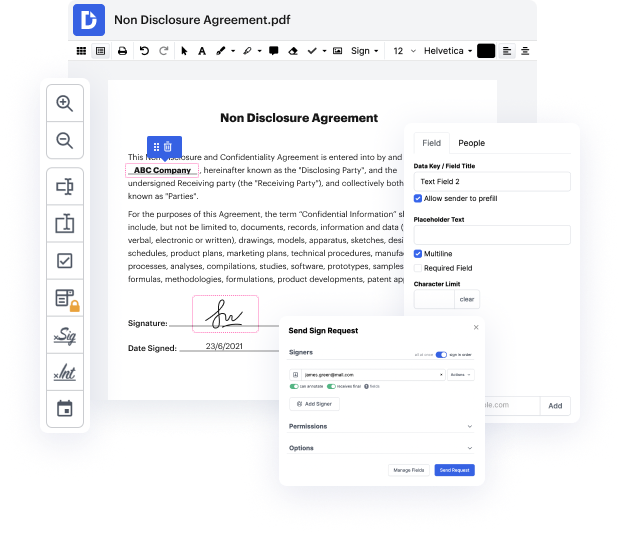
Try DocHub for efficient document management, regardless of your document’s format. It has potent online editing instruments that streamline your document management operations. You can easily create, edit, annotate, and share any file, as all you need to access these features is an internet connection and an functioning DocHub account. A single document solution is everything required. Don’t lose time jumping between different programs for different files.
Enjoy the efficiency of working with a tool made specifically to streamline document processing. See how easy it is to edit any document, even when it is the first time you have worked with its format. Sign up an account now and enhance your whole working process.
all right right bone here and im back with another video and today were going to take a look at cobalt strike and the cobalt strike beacons that come through powershell im consistently seeing this as an attack technique that adversaries are doing threat groups are doing they will use powershell to load a cobalt strike beacon but what we can do with the powershell that we can receive as our with our logs is reverse engineer the location of the c2 server whether that be a named pipe if its an smb listener or whether it be an https server or dns server but lets go ahead we will put a powershell beacon on one of our hosts and then well reverse engineer it with cyber chef so lets go and start doing that so were going to go over here to attacks packages in payload generator and then were going to choose our output our output is going to be powershell command and well choose our https listener here so im going to choose that and well use 64-bit payload were going to go ahead and
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



