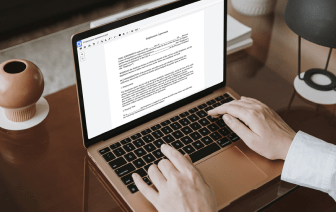

Searching for a specialized tool that deals with particular formats can be time-consuming. Despite the vast number of online editors available, not all of them support CWK format, and definitely not all enable you to make adjustments to your files. To make matters worse, not all of them provide the security you need to protect your devices and paperwork. DocHub is a great answer to these challenges.
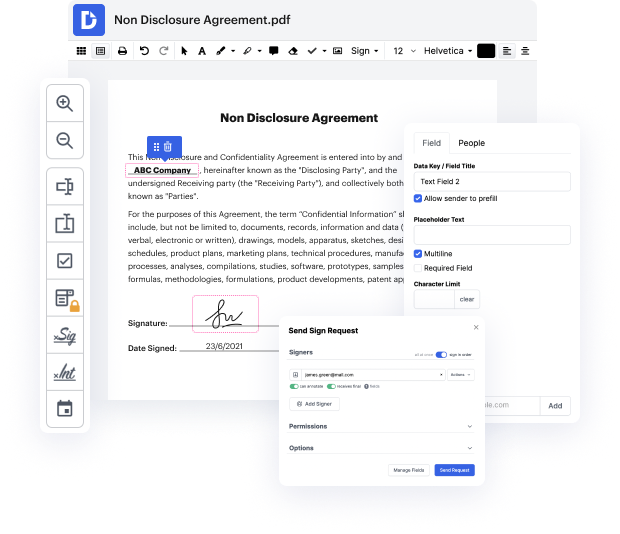
DocHub is a well-known online solution that covers all of your document editing requirements and safeguards your work with enterprise-level data protection. It works with different formats, including CWK, and allows you to edit such paperwork quickly and easily with a rich and user-friendly interface. Our tool fulfills crucial security certifications, like GDPR, CCPA, PCI DSS, and Google Security Assessment, and keeps improving its compliance to provide the best user experience. With everything it offers, DocHub is the most reputable way to Snip PII in CWK file and manage all of your personal and business paperwork, no matter how sensitive it is.
Once you complete all of your modifications, you can set a password on your updated CWK to make sure that only authorized recipients can open it. You can also save your document with a detailed Audit Trail to see who made what edits and at what time. Opt for DocHub for any paperwork that you need to edit securely. Sign up now!
[Music] hi everyone this is sarah and shane welcome to episode 9 of our scenario based demo series today well be discussing service side auto labeling however before we get into the actual details of what were really focusing on today i didnt want to go through a brief agenda so everybody could have an understanding of what will be covered right so of course were going to be going through a recap of what happened last time in our episode client based auto labeling were gonna then jump on over into overall what is service side labeling some of the recent updates that we announced and then of course going into a demo with one of my colleagues so all right so lets go ahead and jump into the recap of last episode right so first of all we did go through the background of what is client-side auto-labeling and then we went through the steps of kind of what is required in our custom sensitive information type for for our code scenario in our test environment in general and then we walk t