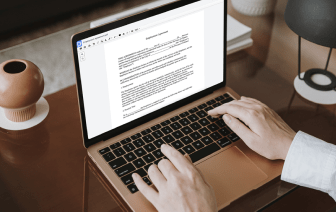
Document generation and approval are a core focus for each organization. Whether handling large bulks of documents or a distinct contract, you have to stay at the top of your efficiency. Choosing a perfect online platform that tackles your most typical papers creation and approval problems might result in a lot of work. A lot of online platforms provide just a limited set of editing and eSignature functions, some of which might be useful to handle ACL file format. A platform that handles any file format and task would be a excellent option when picking software.
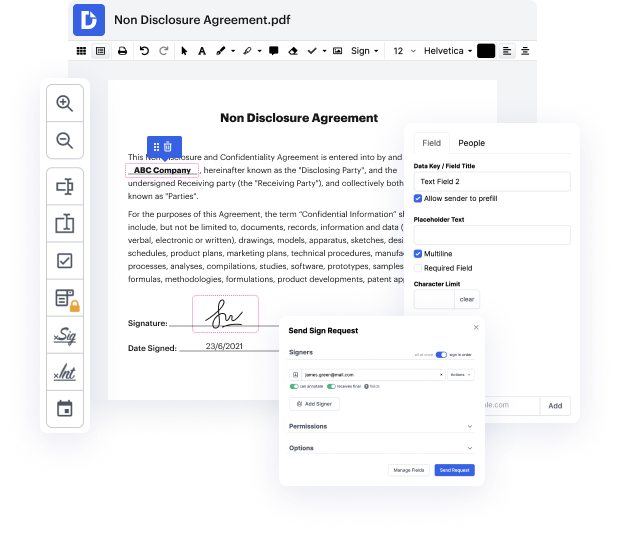
Get document administration and creation to another level of efficiency and sophistication without picking an difficult program interface or costly subscription plan. DocHub offers you instruments and features to deal efficiently with all of document types, including ACL, and perform tasks of any complexity. Edit, manage, that will create reusable fillable forms without effort. Get total freedom and flexibility to slide subject in ACL anytime and securely store all your complete documents in your profile or one of several possible incorporated cloud storage space platforms.
DocHub offers loss-free editing, signature collection, and ACL administration on the professional level. You do not have to go through tiresome guides and invest countless hours figuring out the platform. Make top-tier secure document editing a regular process for your everyday workflows.
hello this is Edie from practical martinet welcome to a new video series where Im going to teach you about access control lists this series is meant to be the last set of videos youll ever have to watch to understand this concept this is the first video in the series where we will be answering the fundamental question what are access lists at its core an access control list is simply a tool you use to identify traffic how you apply the access list then determines what the access list is actually doing for example if you apply an axle issed to an interface then any traffic that is identified by your access list is being permitted through that interface this is the most common application of an ax list but there are many other use cases for a nexus for example if you apply an access list to a network address translation configuration then whatever traffic is identified by the X list is processed through a net if you apply an X list to a VPN configuration then whatever traffic you iden