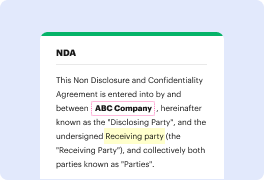
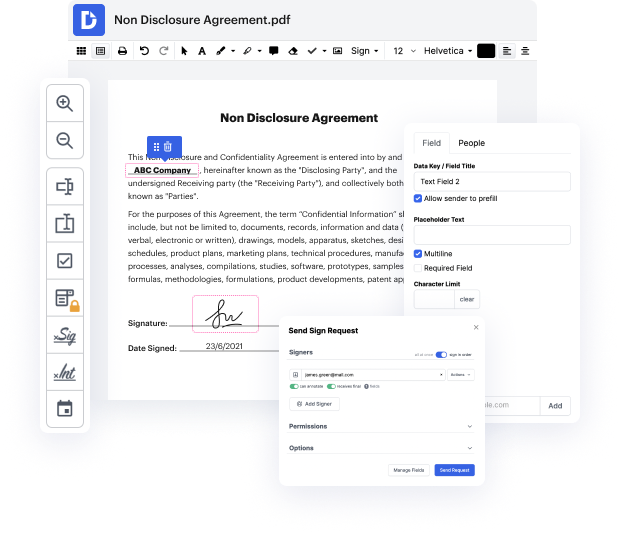
Document generation and approval certainly are a central focus of each organization. Whether dealing with sizeable bulks of files or a particular contract, you must remain at the top of your productiveness. Choosing a excellent online platform that tackles your most common record creation and approval problems might result in quite a lot of work. Many online platforms offer merely a restricted list of editing and signature functions, some of which could possibly be useful to handle AMI format. A platform that handles any format and task might be a excellent choice when selecting application.
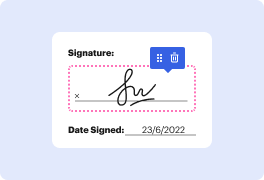
Take file administration and creation to another level of efficiency and sophistication without picking an difficult interface or high-priced subscription plan. DocHub provides you with tools and features to deal effectively with all file types, including AMI, and execute tasks of any complexity. Edit, arrange, and produce reusable fillable forms without effort. Get full freedom and flexibility to set secret in AMI anytime and safely store all of your complete files in your account or one of many possible integrated cloud storage platforms.
DocHub provides loss-free editing, signature collection, and AMI administration on the expert level. You do not need to go through exhausting guides and spend countless hours figuring out the platform. Make top-tier secure file editing a regular practice for your every day workflows.
Hello, welcome to another episode of Back to Basics. My name is Hareesh Singireddy. Im a Solutions Architect here at AWS. Today we are going to talk about managing and protecting secret information needed for your applications to perform its function. This information could be your database passwords, your IAM access keys, your SSH keys, or any other information your application needs to perform its regular function. Here I want to call out two best practices from the AWS Well-Architected Framework security pillar. The first one is, Store Retrieve these secured secrets. The second one is, Audit Rotate these secrets securely and frequently. Lets take a common scenario. You have an application that needs to communicate with the database. So to open a connection to the database, it needs database connection information, like the database server name, database port number, and secret information like database username and database password. So lets take a look at the architectur