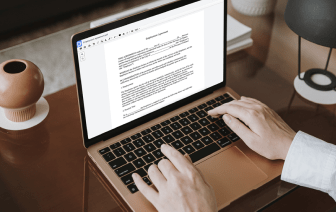
When your daily work consists of lots of document editing, you realize that every file format needs its own approach and often particular software. Handling a seemingly simple ACL file can sometimes grind the whole process to a stop, especially if you are attempting to edit with inadequate software. To avoid this kind of problems, find an editor that can cover all of your needs regardless of the file extension and set attribute in ACL with zero roadblocks.
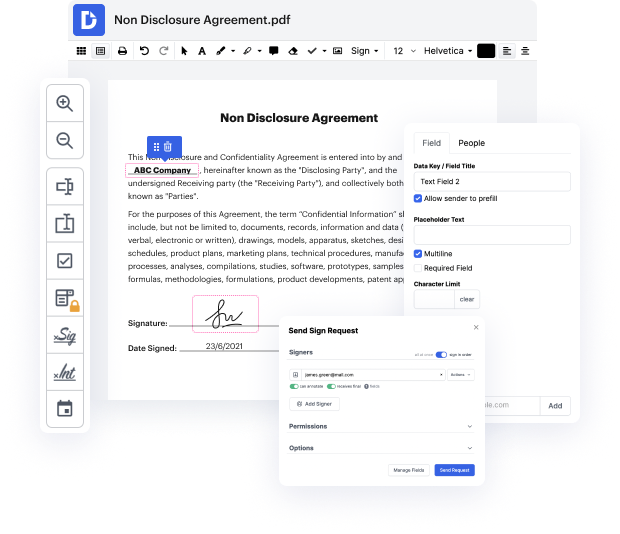
With DocHub, you will work with an editing multitool for any occasion or file type. Minimize the time you used to spend navigating your old software’s features and learn from our intuitive interface while you do the work. DocHub is a efficient online editing platform that handles all of your file processing needs for any file, including ACL. Open it and go straight to efficiency; no prior training or reading guides is required to enjoy the benefits DocHub brings to document management processing. Begin with taking a few minutes to register your account now.
See improvements within your document processing immediately after you open your DocHub account. Save time on editing with our single solution that will help you be more productive with any document format with which you need to work.
The national cyber community center of excellence at NIST has collaborated with private industry to demonstrate a flexible solution for assigning access to information systems, attribute based access control or ABAC. With ABAC, access is assigned based on attributes or characteristics about the subject making the access request, about the file or resource object being requested and environmental conditions. Granular policies can then be established on a combination of these attributes to grant or deny access. Take Linda, an auditor at a large accounting firm. Theyve taken on a new client and established a project team. As a member of the team, Linda will need access to internal documents as well as access to the clients financial records. Under a role based system, the organization would create a role to represent general access to files for team members and the second role for the privileged access that auditors need to view sensitive financial information. Each role would then nee