It is usually difficult to find a solution that can deal with all your company needs or offers you correct instruments to control document creation and approval. Picking an application or platform that includes important document creation instruments that streamline any process you have in mind is crucial. Although the most in-demand file format to use is PDF, you require a comprehensive software to manage any available file format, including rtf.
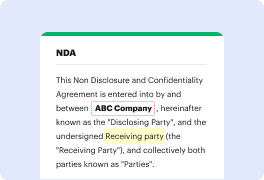
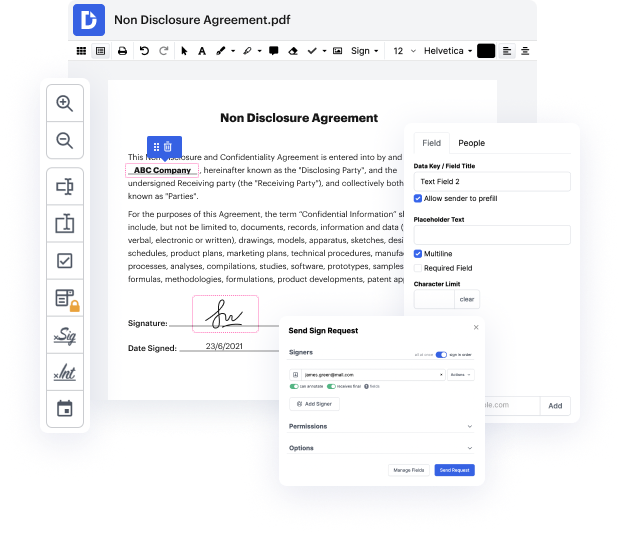
DocHub ensures that all your document creation needs are taken care of. Modify, eSign, rotate and merge your pages according to your requirements with a mouse click. Work with all formats, including rtf, successfully and quick. Regardless of what file format you start dealing with, it is possible to convert it into a needed file format. Save tons of time requesting or looking for the right document format.
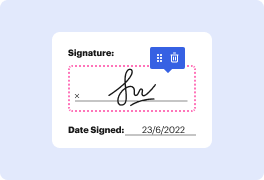
With DocHub, you do not require additional time to get used to our interface and editing procedure. DocHub is an intuitive and user-friendly platform for everyone, even all those with no tech education. Onboard your team and departments and change document managing for the business forever. restore signature in rtf, generate fillable forms, eSign your documents, and have things finished with DocHub.
Benefit from DocHub’s extensive feature list and swiftly work with any document in every file format, such as rtf. Save your time cobbling together third-party solutions and stay with an all-in-one platform to further improve your everyday operations. Start your cost-free DocHub trial right now.
A cryptographic hash allows you to take any amount of data-- it can be a small bit of text, or it can be an entire book-- and you can represent that bit of data as a short string of text. We refer to this short string of hashed text as a message digest. A hash is not an encrypted version of the original text. Its really a one-way trip. Theres no way to recover the original text by simply looking at the hashed value. Its because of this unique characteristic that we commonly use hashes to store passwords. That way, we can compare a stored hash against another hash thats given to us later, but well still have no idea what the original password was from the user. We might also use hashes to confirm that a file that weve downloaded is identical to the original version of that file. And we use hashing during the creation of a digital signature that allows us to provide authentication, non-repudiation, and integrity to a particular document. A fundamental characteristic of hashing alg
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



