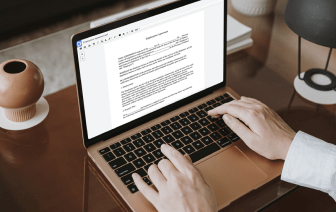
Document generation and approval certainly are a key focus of every organization. Whether working with sizeable bulks of files or a particular contract, you should stay at the top of your efficiency. Finding a ideal online platform that tackles your most frequentl papers generation and approval difficulties could result in quite a lot of work. A lot of online platforms offer you just a limited set of editing and signature features, some of which could possibly be beneficial to handle RPT format. A solution that deals with any format and task would be a superior option when deciding on software.
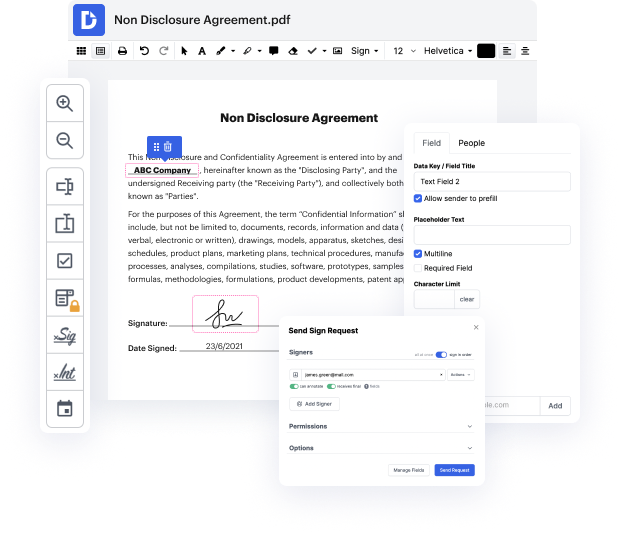
Get document managing and generation to another level of straightforwardness and sophistication without opting for an awkward program interface or high-priced subscription options. DocHub provides you with instruments and features to deal efficiently with all of document types, including RPT, and perform tasks of any complexity. Modify, organize, and make reusable fillable forms without effort. Get complete freedom and flexibility to restore signature in RPT at any time and securely store all your complete files within your account or one of many possible incorporated cloud storage platforms.
DocHub offers loss-free editing, signature collection, and RPT managing on a expert levels. You don’t have to go through tedious tutorials and invest countless hours figuring out the platform. Make top-tier secure document editing a typical practice for your every day workflows.
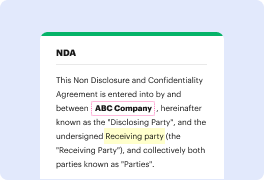
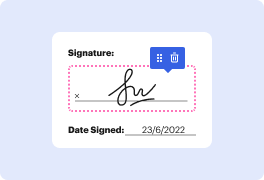
A cryptographic hash allows you to take any amount of data-- it can be a small bit of text, or it can be an entire book-- and you can represent that bit of data as a short string of text. We refer to this short string of hashed text as a message digest. A hash is not an encrypted version of the original text. Its really a one-way trip. Theres no way to recover the original text by simply looking at the hashed value. Its because of this unique characteristic that we commonly use hashes to store passwords. That way, we can compare a stored hash against another hash thats given to us later, but well still have no idea what the original password was from the user. We might also use hashes to confirm that a file that weve downloaded is identical to the original version of that file. And we use hashing during the creation of a digital signature that allows us to provide authentication, non-repudiation, and integrity to a particular document. A fundamental characteristic of hashing alg