Whether you are already used to working with jpg or handling this format the very first time, editing it should not feel like a challenge. Different formats may require particular applications to open and edit them effectively. Yet, if you need to swiftly replace password in jpg as a part of your typical process, it is advisable to get a document multitool that allows for all types of such operations without the need of additional effort.
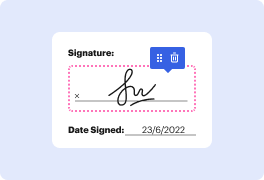
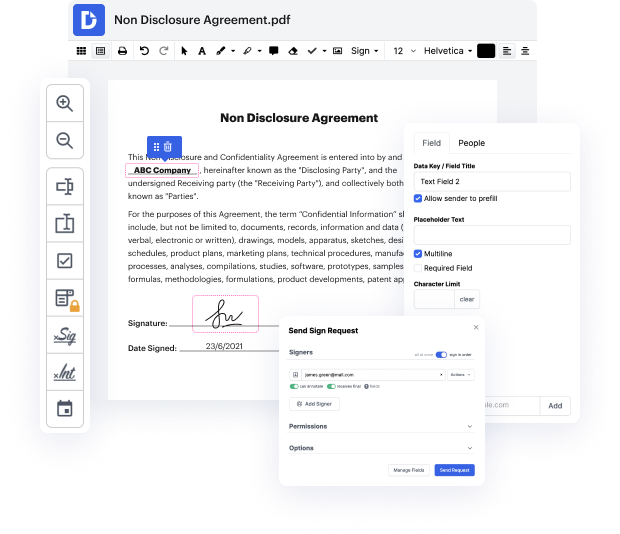
Try DocHub for sleek editing of jpg and other document formats. Our platform offers easy document processing no matter how much or little prior experience you have. With all tools you have to work in any format, you will not have to switch between editing windows when working with each of your papers. Effortlessly create, edit, annotate and share your documents to save time on minor editing tasks. You’ll just need to sign up a new DocHub account, and you can begin your work instantly.
See an improvement in document processing efficiency with DocHub’s simple feature set. Edit any document quickly and easily, irrespective of its format. Enjoy all the benefits that come from our platform’s simplicity and convenience.
[Music] what is going on guys welcome back in todays video were going to learn how to hide information inside of jpeg files and this goes beyond basic stuff like strings numbers or any other primitive data types were going to be able to hide fully executable programs inside of jpeg files without changing the image without changing anything about the image functionality its still a normal photo its still a normal jpeg file but it has some information in it that we can then also extract again and in order to show you how you can do that were going to use this image here so this is a basic jpeg file an image of a woman taking a picture with a camera and all that uh you can see the extension here is jpeg literally every jpeg file that is a normal jpeg file will work for this so you dont have to pick a special one um and were going to look at the bytes of the jpeg file in order to see why we can do that and how we can do that now in order to look at the bytes were not going to use
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



