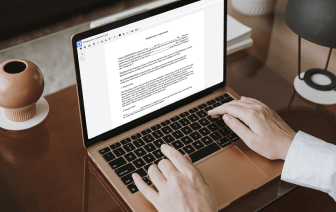
It is often hard to find a solution that may deal with all of your company demands or will provide you with correct instruments to handle document generation and approval. Picking a software or platform that includes essential document generation instruments that simplify any process you have in mind is vital. Even though the most popular formatting to work with is PDF, you need a comprehensive solution to deal with any available formatting, such as OMM.
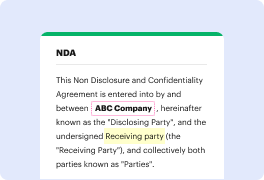
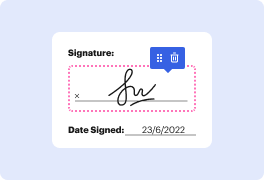
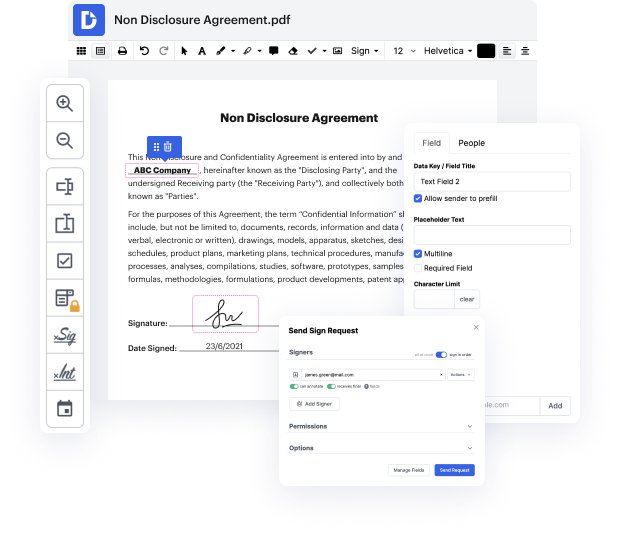
DocHub helps to ensure that all of your document generation requirements are taken care of. Revise, eSign, rotate and merge your pages in accordance with your requirements with a mouse click. Deal with all formats, such as OMM, successfully and . Regardless of what formatting you begin working with, it is possible to transform it into a required formatting. Preserve a lot of time requesting or looking for the correct document type.
With DocHub, you don’t need more time to get comfortable with our user interface and modifying procedure. DocHub is surely an easy-to-use and user-friendly software for anyone, even those with no tech background. Onboard your team and departments and transform file administration for your firm forever. remove type in OMM, create fillable forms, eSign your documents, and have things carried out with DocHub.
Reap the benefits of DocHub’s comprehensive feature list and quickly work with any file in any formatting, including OMM. Save time cobbling together third-party software and stick to an all-in-one software to further improve your everyday procedures. Begin your free of charge DocHub trial subscription right now.
Hello, everyone! In this video were gonna talk about the different wireless security methods and protocols that are used in wireless networks. Now most of us had connected to a Wi-Fi network with our laptop, tablet, or even our smartphone, and to join that network with our device you had to select a network name and you had to supply a password. Now Wi-Fi networks can be just open with no password required, so that means that anybody can join it. However in the majority of cases Wi-Fi networks will be secure and will require a password. Now there are several different protocols that are used for securing a Wi-Fi network. So lets start with a secure protocol called WEP WEP or Wired Equivalent Privacy was developed in 1999 and its the earliest security protocol that was used for wireless networks. And also as its name implies its meant to supply the same security to wireless networks as it did for wired networks. However this turned out not to be the case because after a time it was