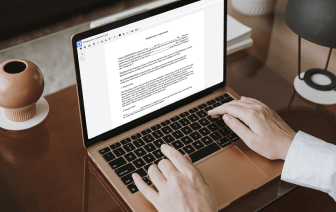
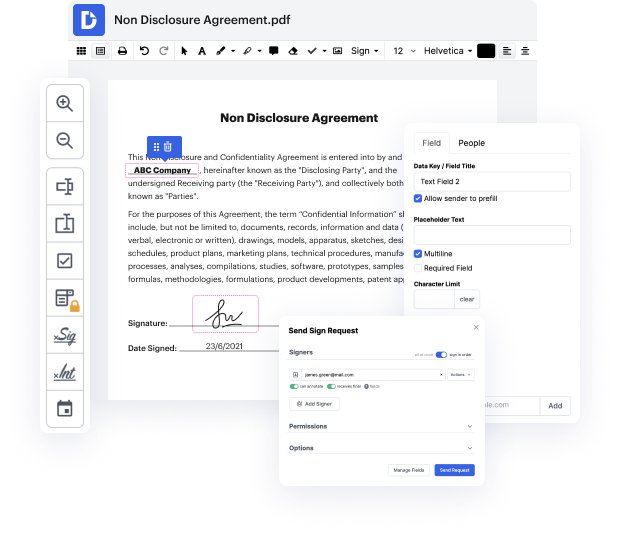
Document generation and approval certainly are a key priority of each business. Whether dealing with large bulks of files or a particular contract, you must stay at the top of your productiveness. Getting a ideal online platform that tackles your most frequentl document generation and approval obstacles may result in quite a lot of work. Many online platforms provide just a restricted list of modifying and eSignature features, some of which could possibly be valuable to manage ACL format. A solution that deals with any format and task might be a excellent choice when picking program.
Get document managing and generation to another level of efficiency and excellence without choosing an cumbersome interface or pricey subscription options. DocHub provides you with tools and features to deal effectively with all of document types, including ACL, and perform tasks of any complexity. Edit, arrange, that will create reusable fillable forms without effort. Get full freedom and flexibility to put in URL in ACL at any time and securely store all your complete documents within your account or one of many possible incorporated cloud storage platforms.
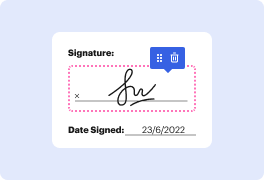
DocHub provides loss-free editing, signature collection, and ACL managing on the expert level. You do not have to go through exhausting tutorials and invest a lot of time finding out the software. Make top-tier secure document editing a standard process for your day-to-day workflows.
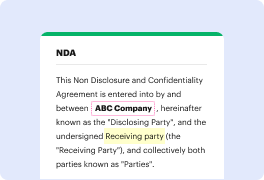
hello and this is sunny welcome back and Internet is a private network which is heavily protected by many different networking devices such as a router firewall proxy server DMZ honeynet IPs and IDs this diagram is an overly simplified version of the reality I try to pull these devices together in a reasonable order only for teaching and learning purpose today my topic is rotters access control list or ACL a [Music] router is used to connect networks together and is primary function is to deliver packets based on layer 3 IP address this is the most important function of a router I will have a separate video talking about the routers today I only focus on one of the routers of security features a CL AC L stands for access control list which is a setup to conquer the traffic in both directions incoming and outgoing a CL tells rodder to permit or deny traffic according to one or more of the following variables source IP address source subnet mask destination IP address destination subnet