COVID forever transformed how businesses look at their internal practices and processes. It impacted enterprises of all sizes and industries, posing new challenges for staying connected. The pandemic indicated that all businesses need to incorporate digital tools into every day routines. They became essential for far more than hybrid working models.
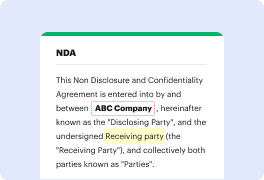
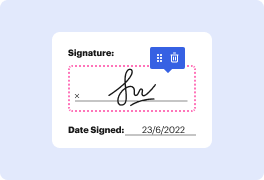
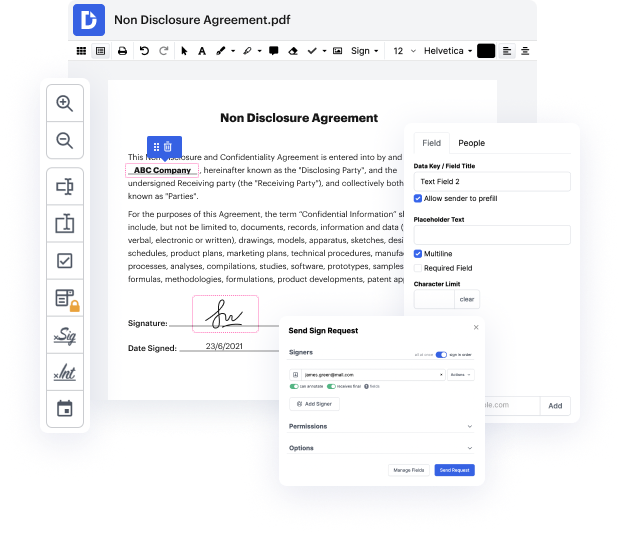
Platforms like DocHub enable you to boost your document administration and approval operations. DocHub is the go-to tool for end-to-end online editing and signatures. It helps reduce your everyday contract and agreement generation and approval tasks. Gain access to PDF Tool - Internet Key Exhange innovative editing features that cover all of your administration demands. Work with any document type and formatting, produce fillable fields, and efficiently collect signatures from your colleagues and customers. No previous training or experience is necessary.
With PDF Tool - Internet Key Exhange, it is possible to maximize the quality of your documents, speed up the approval process, and securely store finished documents. Get yourself a free DocHub account right now and change your plan when you want.
The video tutorial discusses Internet Key Exchange (IKE) in the context of cryptography and network security. It explains how keys are exchanged between sender and receiver to ensure secure communication over a network. IKE is a key management protocol used to establish secure communication between two devices, ensuring that information is not leaked during communication. A new channel on study abroad content is also mentioned in the video description.
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



