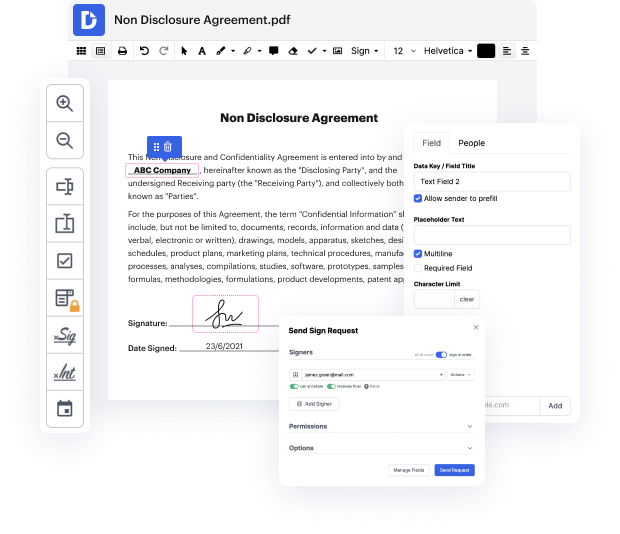
Have you ever had trouble with modifying your Jpg document while on the go? Well, DocHub has an excellent solution for that! Access this cloud editor from any internet-connected device. It enables users to Omit tag in Jpg files rapidly and anytime needed.
DocHub will surprise you with what it offers. It has robust functionality to make whatever changes you want to your paperwork. And its interface is so simple-to-use that the whole process from start to finish will take you only a few clicks.
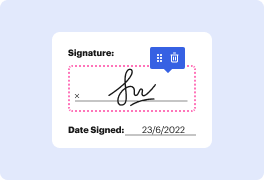
As soon as you complete adjusting and sharing, you can save your updated Jpg file on your device or to the cloud as it is or with an Audit Trail that contains all modifications applied. Also, you can save your paperwork in its original version or transform it into a multi-use template - complete any document management task from anywhere with DocHub. Sign up today!
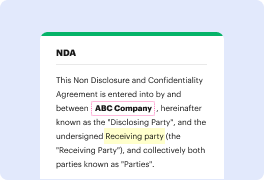
if youve been curious about the hacker applications of steganography today well show you a technique to hide and then execute a payload in an image file on this episode of cyberweapons lab [Applause] [Music] steganography is a practice of hiding things in an image and in previous episodes weve covered how to do this but today were going to take it a step further and actually attempt to execute code that weve hidden inside an image now why might we want to do this well there are actually instances of botnets being controlled by checking a twitter feed and then downloading an image that controls hidden command tags and this is interesting because typically the way that a malware researcher would find something like this is by focusing on the communication between the command and control server and infected computers by instead directing the traffic to a public ip address like twitter youd be able to get around your ip getting flagged and all your bots getting taken down which is a
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



