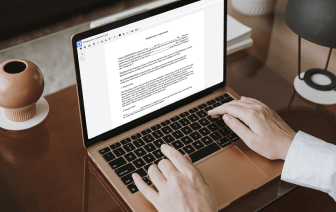
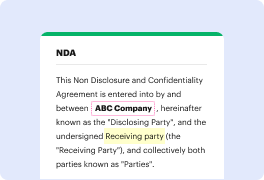
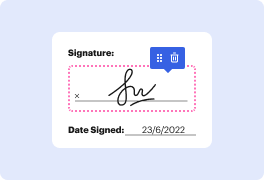
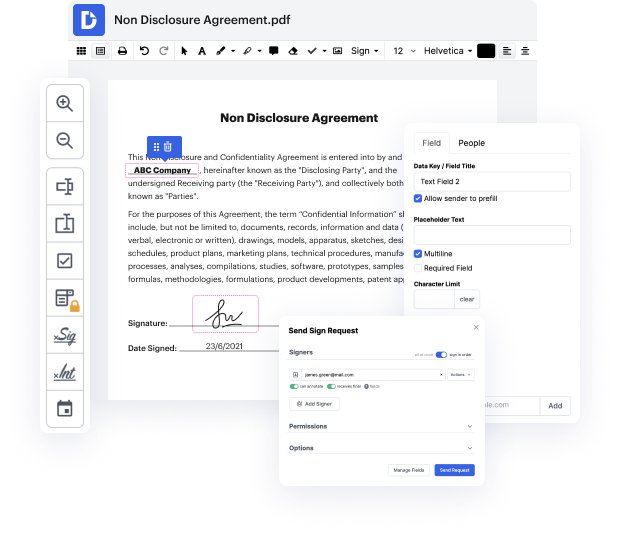
DocHub makes it fast and simple to omit shadow in rtf. No need to download any software – simply add your rtf to your profile, use the easy drag-and-drop interface, and quickly make edits. You can even use your desktop or mobile device to modify your document online from any place. That's not all; DocHub is more than just an editor. It's an all-in-one document management solution with form constructing, eSignature capabilities, and the option to allow others fill out and sign documents.
Every file you upload you can find in your Documents folder. Create folders and organize records for easier search and retrieval. Furthermore, DocHub ensures the safety of all its users' information by complying with strict protection protocols.
hey everyone brockpon here and iamp;#39;m back with another video and today weamp;#39;re going to take a look at shadow credentials so what are shadow credentials shadow credentials are when you can push a key into a system or a user account and then authenticate to it it sounds crazy but it is entirely possible weamp;#39;re going to use a tool called whisker to do this today but to make sure that you have the right permissions to do this in act directory you need to have a specific user group attached to the user that youamp;#39;ve compromised in this case if youamp;#39;re looking through bloodhound scans and you have found a user with the key admins group youamp;#39;ll then be able to do this attack but letamp;#39;s take a look at clint here our typical victim and if we just do net user clint dot barton and then we go domain we will see he is part of enterprise key admins and key admins right outside of that heamp;#39;s just a domain user right you may be a local administrato