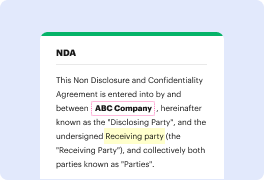
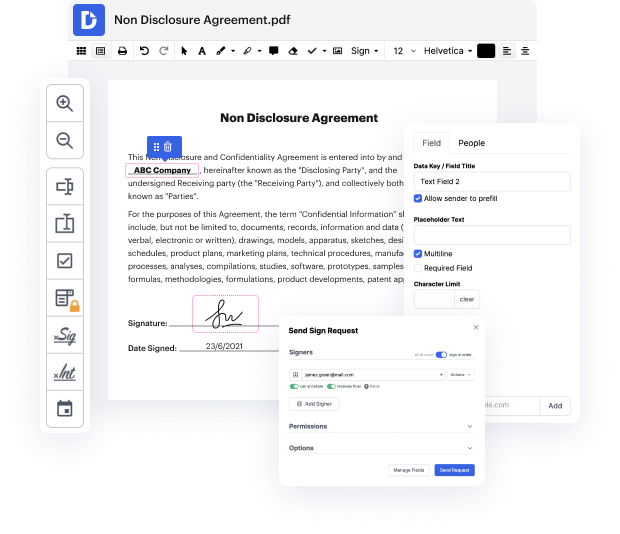
Selecting the ideal document management solution for your organization might be time-consuming. You have to assess all nuances of the app you are interested in, evaluate price plans, and stay vigilant with safety standards. Arguably, the ability to work with all formats, including TXT, is vital in considering a platform. DocHub provides an vast list of capabilities and instruments to successfully deal with tasks of any complexity and take care of TXT formatting. Get a DocHub profile, set up your workspace, and start working on your files.
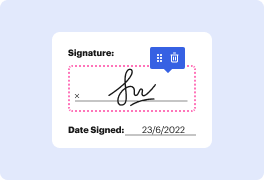
DocHub is a thorough all-in-one platform that permits you to change your files, eSign them, and make reusable Templates for the most commonly used forms. It provides an intuitive interface and the ability to deal with your contracts and agreements in TXT formatting in a simplified mode. You do not have to worry about reading numerous tutorials and feeling stressed out because the software is too sophisticated. omit password in TXT, assign fillable fields to specified recipients and gather signatures effortlessly. DocHub is about effective capabilities for specialists of all backgrounds and needs.
Increase your document generation and approval procedures with DocHub right now. Benefit from all of this using a free trial and upgrade your profile when you are ready. Edit your files, create forms, and find out everything you can do with DocHub.
hi and welcome back to another episode on how to hack and today well be learning about how you can get access into a system without trying Brute Force attacks [Music] yes I know this sounds crazy but it can absolutely be done you just really have to understand how those applications store their passwords and credentials and all you got to do then is just to replay the password into the login field and thats it it came over and remember kids hacking is legal if you want to hack do not try to hack against hacker law because hacker law can fire IP address your password and everything about you and the reason why this can be happening is because one there is another vulnerable service within the target server and the hacker gained access over into the service and after which the hacker then go over into the listing of the photos directory and the final that okay in this particular other service there is a config folder and in a config folder they store all these different credentials li
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



