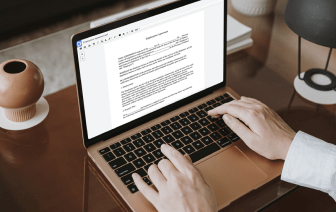
Disadvantages exist in every tool for editing every file type, and despite the fact that you can use many solutions on the market, not all of them will suit your specific needs. DocHub makes it much simpler than ever to make and modify, and handle documents - and not just in PDF format.
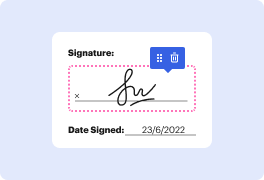
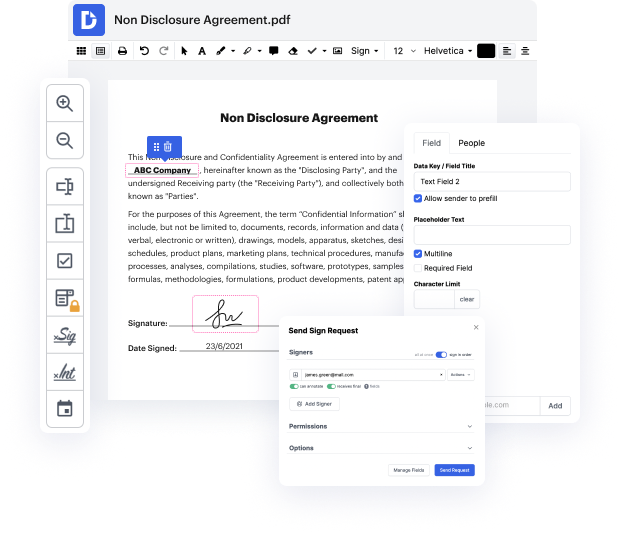
Every time you need to quickly negate authentication in WRI, DocHub has got you covered. You can easily modify form components such as text and pictures, and layout. Personalize, organize, and encrypt paperwork, develop eSignature workflows, make fillable forms for intuitive information gathering, and more. Our templates feature enables you to generate templates based on documents with which you often work.
In addition, you can stay connected to your go-to productivity features and CRM solutions while dealing with your paperwork.
One of the most incredible things about utilizing DocHub is the ability to deal with form tasks of any difficulty, regardless of whether you need a quick modify or more complex editing. It includes an all-in-one form editor, website form builder, and workflow-centered features. In addition, you can rest assured that your documents will be legally binding and comply with all protection frameworks.
Cut some time off your projects with the help of DocHub's tools that make handling paperwork straightforward.
[Applause] hello everybody welcome back to another episode of rethinking connectivity my name is jeremy and today weamp;#39;re going to be going over the authentication and authorization model inside of nats essentially our security model now this is a really big topic to cover but i figured weamp;#39;ve gotten a lot of requests for us to cover it so today weamp;#39;re going to dive in deep and iamp;#39;m going to go over the overall architecture and some of the design choices that we made around building a security model like this and then weamp;#39;re going to dive in and weamp;#39;re going to actually sketch one out iamp;#39;m using a tool called nsc and applying it to our nat server and i could show you all the different ways that you can kind of lock down certain accounts that you could share between accounts etc etc so letamp;#39;s dive straight in so what is what is it that we call decentralized off often and off z and gnats well itamp;#39;s a couple of