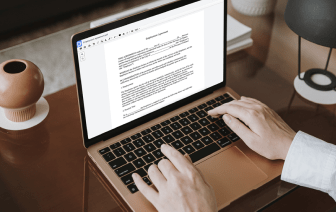
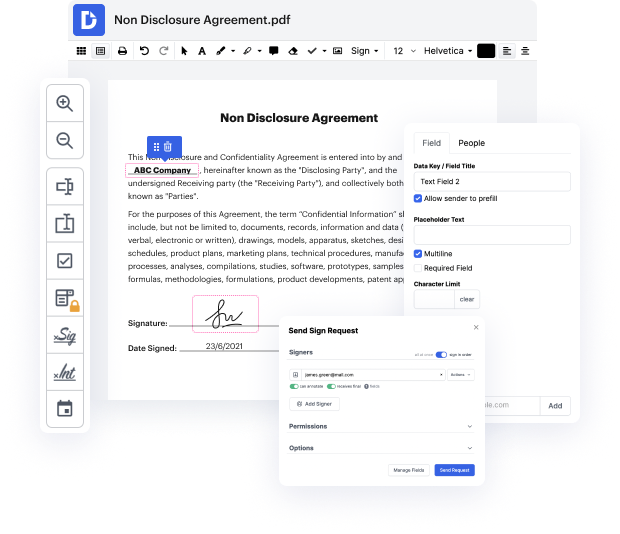
DocHub makes it fast and straightforward to negate authentication in OSHEET. No need to download any software – simply upload your OSHEET to your account, use the simple drag-and-drop editor, and quickly make edits. You can even use your desktop or mobile device to adjust your document online from any place. That's not all; DocHub is more than just an editor. It's an all-in-one document management platform with form building, eSignature features, and the ability to enable others complete and sign documents.
Every file you edit you can find in your Documents folder. Create folders and organize records for easier search and retrieval. Furthermore, DocHub guarantees the safety of all its users' information by complying with stringent protection standards.
Hello everyone, my name is Vikal Jain and today I am going to nullify debit and credit entries in Excel. So, even you can say it as we are going to nullify positive and negative entries. So, here we have 1,000 entries. As you can see on the screen, it is one thousand. Now, we are going to nullify all the entries and we are going to find out the remaining entries which are not nullifying. So, what we are going to do? We are going to do some steps, so that we can extract that data. So letamp;#39;s begin. So for nullifying the entry we are going to use ABS first. So, what ABS do? ABS convert all the number into positive. It will also convert the negative number into positive and positive number into positive. So, letamp;#39;s try ABS. So, drop in down. Now, I am going to sort this data ing to ABS. Abs. Now you can see here is one positive, one negative, one negative, one negative. So, two is nullifying. So, letamp;#39;s try to find out the list. We are going to make a pivot table here.