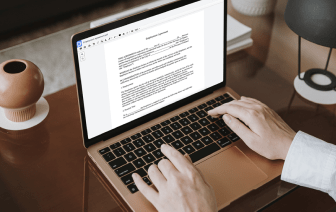
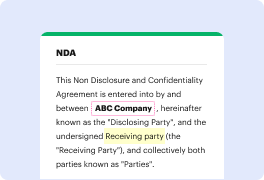
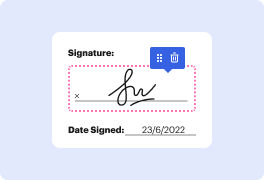
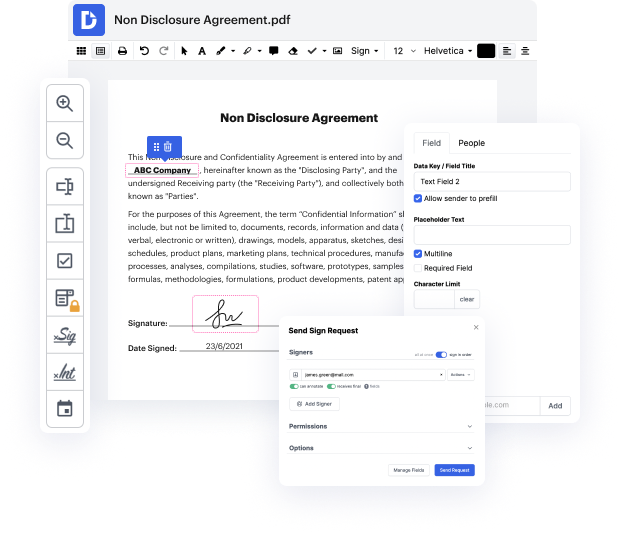
DocHub is an all-in-one PDF editor that allows you to negate authentication in 600, and much more. You can underline, blackout, or erase document elements, insert text and pictures where you need them, and collect data and signatures. And since it runs on any web browser, you won’t need to update your hardware to access its powerful tools, saving you money. With DocHub, a web browser is all you need to manage your 600.
Log in to our website and follow these guidelines:
It couldn't be simpler! Streamline your document processing today with DocHub!
Iamp;#39;m going to show you how to not get ripped off and buy chillit for those of you that have been following me for a while you know that Iamp;#39;m an advocate for chillit Iamp;#39;ve tried out most brands now Iamp;#39;ve had loads of companies docHub out to me and send me their shillig jit there are lots of good ones out there the best one that Iamp;#39;ve been using is rigit itamp;#39;s from rit. co.uk so it has to come in the resin form this is the 20 G let me get the lid off 20 g pack which is quite expensive Iamp;#39;ve spoken extensively with the guys that run this company and theyamp;#39;ve made a 10 G version which is 29 thatamp;#39;s going to last you for a couple of months you donamp;#39;t need to use much Iamp;#39;m going to show you the amount that we use and Iamp;#39;m going to show you it dissolving in the water to make sure that you know that youamp;#39;ve got the real stuff so your shillig jit should smell to carry fiery itamp;#39;s got a very earthy s