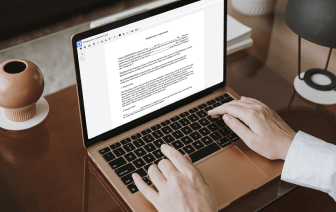
Document generation and approval are a core focus of each firm. Whether handling sizeable bulks of documents or a certain agreement, you need to stay at the top of your efficiency. Getting a perfect online platform that tackles your most frequentl file creation and approval difficulties could result in quite a lot of work. Many online platforms offer you just a limited list of editing and signature functions, some of which may be useful to deal with CWK format. A solution that handles any format and task would be a superior choice when selecting software.
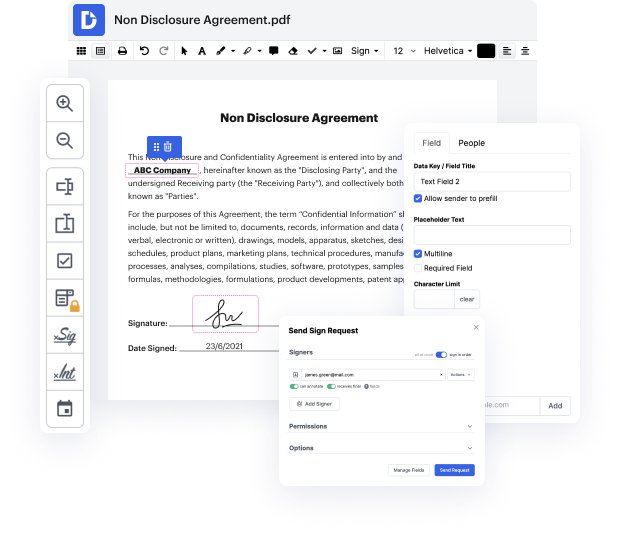
Get file managing and creation to a different level of simplicity and excellence without picking an awkward user interface or pricey subscription plan. DocHub gives you tools and features to deal successfully with all file types, including CWK, and perform tasks of any difficulty. Edit, manage, and create reusable fillable forms without effort. Get complete freedom and flexibility to link trait in CWK anytime and safely store all of your complete documents within your profile or one of many possible integrated cloud storage platforms.
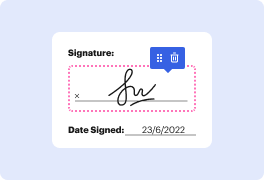
DocHub offers loss-free editing, signature collection, and CWK managing on the professional level. You do not need to go through tiresome guides and spend a lot of time figuring out the software. Make top-tier secure file editing a typical practice for your everyday workflows.
[Music] [Applause] [Music] thank you [Music] okay so thank you I think that in the beginning Ill explain what WS link is oh okay can you hear me fine okay so WS link is uh interesting piece of malware that we like discovered and all of its samples were protected with an interesting virtual machine and our motivation to the obfuscate is for to see what is under the hood of this sample so in the beginning there werent any clear artifacts about we just suggest what the virtual machine was but after the publication of our paper several researchers docHubed out to us and told us that this is something which really looks like old virtualizer which is basically like the virtual machine used in temida and we afterwards like verified and confirm it so well talk like about code virtualizer and it should be fine because it was unpublicly described before as far as I know so I think that now Ill tell something about me so my name iska and Ive been working as a malware researcher at ESET since