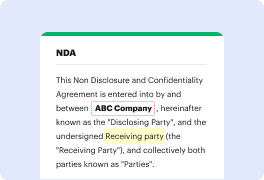
Whether you are already used to working with pdf or managing this format the very first time, editing it should not feel like a challenge. Different formats might require specific software to open and edit them effectively. Yet, if you have to quickly insert token in pdf as a part of your typical process, it is advisable to get a document multitool that allows for all types of such operations without additional effort.
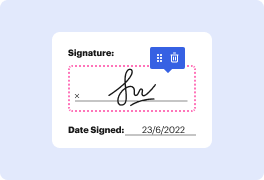
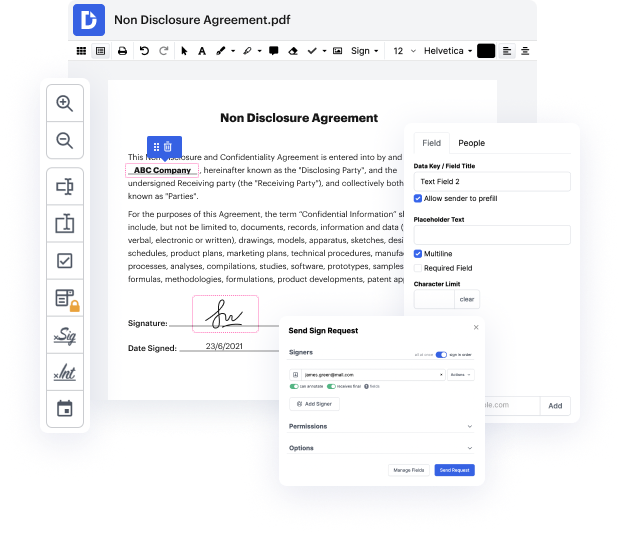
Try DocHub for streamlined editing of pdf and also other file formats. Our platform provides easy papers processing no matter how much or little previous experience you have. With tools you have to work in any format, you will not have to jump between editing windows when working with every one of your papers. Effortlessly create, edit, annotate and share your documents to save time on minor editing tasks. You’ll just need to register a new DocHub account, and then you can begin your work instantly.
See an improvement in document processing efficiency with DocHub’s straightforward feature set. Edit any file quickly and easily, regardless of its format. Enjoy all the advantages that come from our platform’s efficiency and convenience.
okay guys lets start with case number one hijacking via PDF final what I wanted to present to you in this case is how you can hack the web applications with PDF files this is a really great attack because PDF files are everywhere they are are ubiquitous so now imagine that you can upload and malicious PDF files to the web application and then somehow magically you can steal a of the user as a result of processing of this malicious PDF file thats gonna be a great and powerful attack and this is exactly what I want to present to you here so Ive got a demo and the demo for this case is located at training good local slash hijacking in my testing environment so let me go there right now and let me show you how this attack works in practice okay here is my demo for this case and what this demo is all about it is actually about uploading a PDF file and I just want to upload here actually and malicious PDF file okay and this case is about a hijacking via PDF file a
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



