Working with paperwork can be a daunting task. Each format has its peculiarities, which frequently results in confusing workarounds or reliance on unknown software downloads to bypass them. The good news is, there’s a tool that will make this task more enjoyable and less risky.
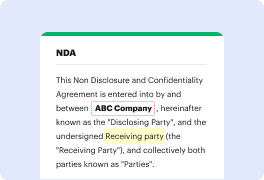
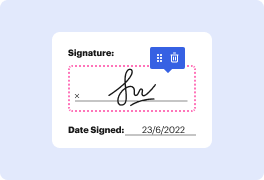
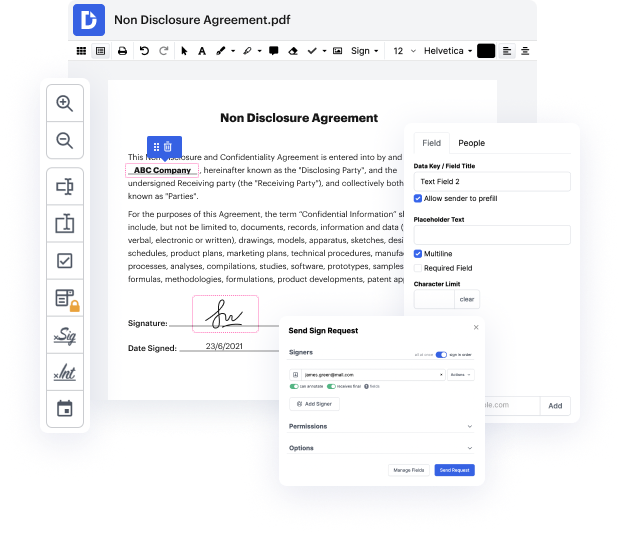
DocHub is a super straightforward yet full-featured document editing program. It has different features that help you shave minutes off the editing process, and the option to Inscribe Seal Title For Free is only a small part of DocHub’s functionality.
Whether if you need occasional editing or to tweak a multi-page document, our solution can help you Inscribe Seal Title For Free and make any other desired changes easily. Editing, annotating, signing and commenting and collaborating on documents is straightforward utilizing DocHub. Our solution is compatible with various file formats - choose the one that will make your editing even more frictionless. Try our editor free of charge today!
whats going on youtube this is ipsec me doing seal from hack the box which involves one of my favorite types of vulnerabilities and thats when theres a big talk about it but theres never really any patch the talking question is from orange sy the server side request forgery king back in black cat 2018 it involves a tomcat server that is running behind a reverse proxy such as engine x and the reverse proxy is trying to block the access of management functions of tomcat such as accessing slash manager html the server side request forgery involves putting a payload in the url that engine x just reads and doesnt do anything with but tomcat will actually remove a portion of that url letting you rebuild the url when it gets to the tomcat application therefore bypassing any um blacklist and then once you get a shell on the box it involves a private via ansible which i just really liked so with that being said lets jump in as always were gonna start off with the nmap so dash sc for def
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



