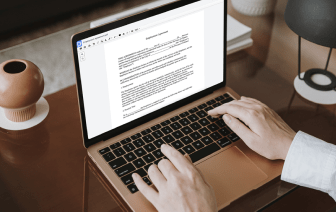
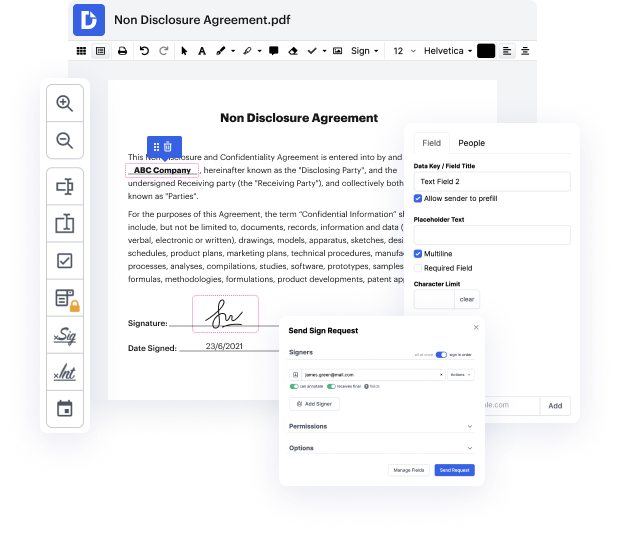
You can’t make document adjustments more convenient than editing your ACL files on the web. With DocHub, you can get tools to edit documents in fillable PDF, ACL, or other formats: highlight, blackout, or erase document elements. Add text and images where you need them, rewrite your form entirely, and more. You can download your edited record to your device or share it by email or direct link. You can also transform your documents into fillable forms and invite others to complete them. DocHub even offers an eSignature that allows you to sign and deliver documents for signing with just a couple of clicks.
Your records are securely stored in our DocHub cloud, so you can access them anytime from your PC, laptop, mobile, or tablet. Should you prefer to use your mobile device for file editing, you can easily do it with DocHub’s mobile app for iOS or Android.
hello everyone thank you for watching this video in which I will answer a question regarding ACS with spring security and the way to configure security at the domain level so the question was about what is a CL when do we use this here for example together or without having also on the endpoint base security and basically the fact is that ACS are pretty difficult and they represent the most granular from my point of view the most granular way to apply security to apply security at the record level or at the instance level of an object we can call it more generally usually it applies to things that are stored in the database so thatamp;#39;s why I basically refer to the database thatamp;#39;s why the only and main implementation of a CL at the moment is the JDBC implementation that means that the ACS are managed in the database and they usually refer to things that are stored in the database but if you want to see them at the more general level like a more general picture of them the