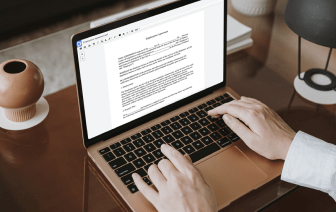
Whether you are already used to working with xml or handling this format for the first time, editing it should not seem like a challenge. Different formats might require particular applications to open and edit them effectively. Nevertheless, if you need to quickly inject sentence in xml as a part of your typical process, it is advisable to get a document multitool that allows for all types of such operations without the need of extra effort.
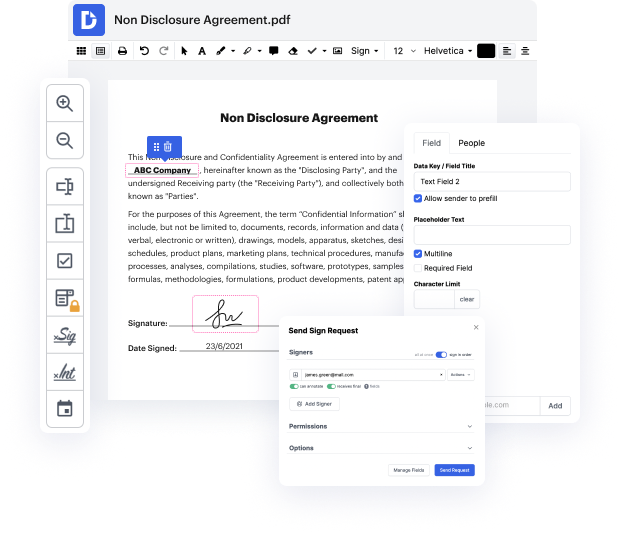
Try DocHub for streamlined editing of xml and also other document formats. Our platform offers straightforward papers processing no matter how much or little prior experience you have. With all tools you have to work in any format, you won’t have to switch between editing windows when working with every one of your documents. Easily create, edit, annotate and share your documents to save time on minor editing tasks. You will just need to sign up a new DocHub account, and you can start your work right away.
See an improvement in document processing productivity with DocHub’s simple feature set. Edit any document easily and quickly, regardless of its format. Enjoy all the benefits that come from our platform’s simplicity and convenience.
A code injection attack is when the attacker puts their own code into an existing data stream. This is often enabled because of bad programming with an application. An application shouldnt allow you to put your own code into a data stream. But, often, the code is not checked by the application, and attackers are able to exploit that vulnerability. Theres many different types of code that you can inject. You can inject HTML, or LDAP, or SQL code-- and any one of those may be able to manipulate or gather information from a machine, especially if you have control over the type of code that you would put into that data stream. One very common code injection type is a SQL injection. SQL stands for Structured Query Language-- or SQL. This is a very common relational database used on many websites. If you can circumvent the web front end, then you can gain access to the data thats in that database. Of course, the web front end should not allow these types of requests, but if the input is