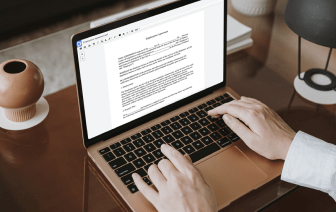
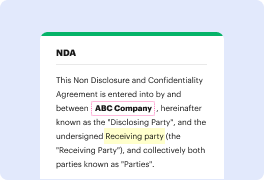
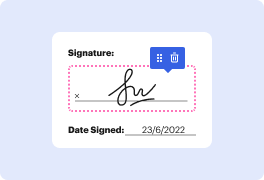
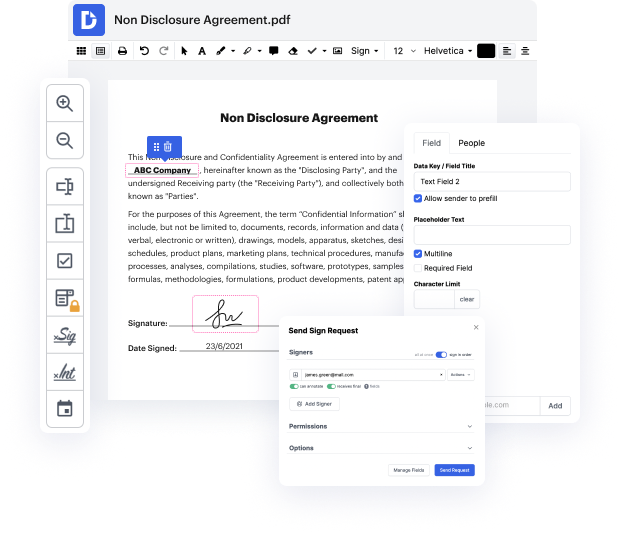
With DocHub, you can easily inject PII in LOG from anywhere. Enjoy capabilities like drag and drop fields, editable text, images, and comments. You can collect eSignatures securely, add an extra level of defense with an Encrypted Folder, and collaborate with teammates in real-time through your DocHub account. Make changes to your LOG files online without downloading, scanning, printing or mailing anything.
You can find your edited record in the Documents folder of your account. Manage, submit, print out, or turn your document into a reusable template. With so many advanced features, it’s easy to enjoy trouble-free document editing and management with DocHub.
my name is Olaf Iamp;#39;m a Solutions Architect on our professional services team and I want to talk a little bit about PII data set the stage a little bit about wide may matter and then in more detail how it pertains to the data that you guys are sending to zoom all right with new regulations you know sort of coming out in the last couple of years and I think this topic becomes more and more important so this here is the description of personal data from the gdpr framework Iamp;#39;m not going to read the whole thing so Iamp;#39;m gonna give you a second to read it what stands out to me when reading this is for one itamp;#39;s itamp;#39;s really ambiguous and it can mean many many different things so itamp;#39;s not entirely clear how to interpret this I believe at the end of the day everybody in terms of gdpr is sort of waiting for the first couple of for the first couple of companies that gets and like get caught up in something and to see how the courts rule and how this law