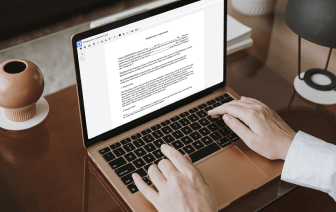
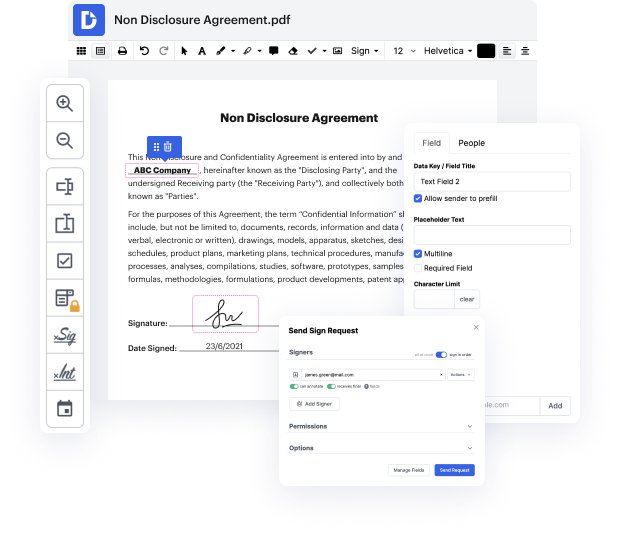
Many people find the process to inject outline in LOG rather daunting, especially if they don't often deal with documents. Nevertheless, today, you no longer have to suffer through long instructions or spend hours waiting for the editing software to install. DocHub lets you change forms on their web browser without installing new applications. What's more, our feature-rich service offers a complete set of tools for professional document management, unlike so many other online tools. That’s right. You no longer have to export and import your templates so often - you can do it all in one go!
Whatever type of document you need to adjust, the process is straightforward. Benefit from our professional online service with DocHub!
hello and welcome to secure code warrior in this module weamp;#39;ll be looking at LDAP injection will explain what LDAP injection is its causes and Preventionamp;#39;s and some potential hazards so what is an LDAP injection an LDAP injection is a vulnerability by which an attacker can influence back-end LDAP queries by injecting malicious LDAP statements via user controllable input what causes an LDAP injection user input is used to dynamically build LDAP queries if this input is not first validated the LDAP query interpreter can be tricked into running arbitrary queries to understand the LDAP injection vulnerability letamp;#39;s look at an example of an authentication bypass here an attacker submits input values that will take advantage of a back-end LDAP statement used to query users and passwords the submitted input changes the logic of the query the ampersand in parentheses is interpreted as a true statement because of this additional true statement the password condition will