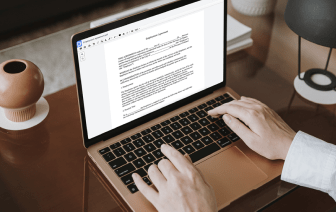
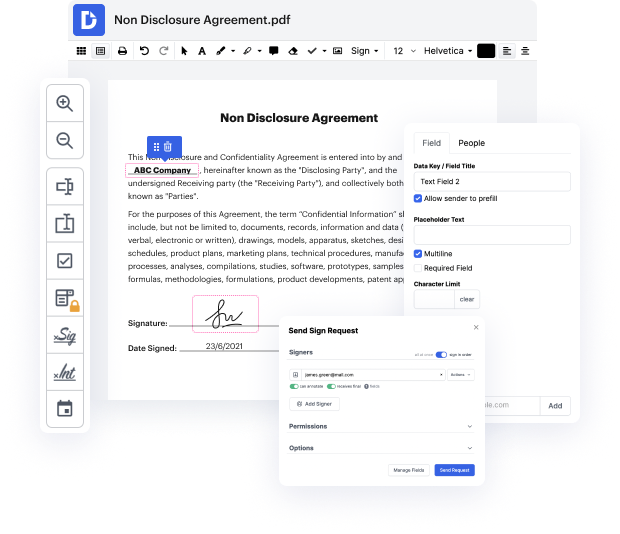
Many people find the process to inject issue in LOG quite daunting, especially if they don't regularly work with paperwork. Nonetheless, today, you no longer have to suffer through long instructions or wait hours for the editing software to install. DocHub lets you modify forms on their web browser without installing new applications. What's more, our robust service offers a complete set of tools for professional document management, unlike so many other online solutions. That’s right. You no longer have to export and import your forms so frequently - you can do it all in one go!
No matter what type of paperwork you need to alter, the process is easy. Take advantage of our professional online service with DocHub!
dependency injection in one sentence was perfectly described by james shore it means giving an object its instance variables but because i know that you are still confused letamp;#39;s take a closer look what actually are dependencies here well these are objects a specific class depends on letamp;#39;s take a look at this computer to be able to run properly it needs a processor ram a hard drive and a graphics card so these single components are the computeramp;#39;s dependencies because the computer depends on these components if we think of this computer now as a class in programming we could either create the single components in the computer class or we could create them somewhere else letamp;#39;s take a look what happens if we create them in the computer class this would mean every computer that we create has the same specs and if we change for example the hard drive it will be changed for all computers this is bad dependency injection solves this problem one way of injecting