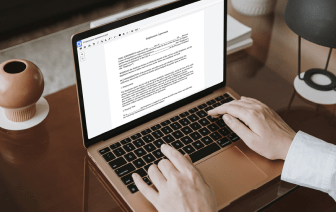

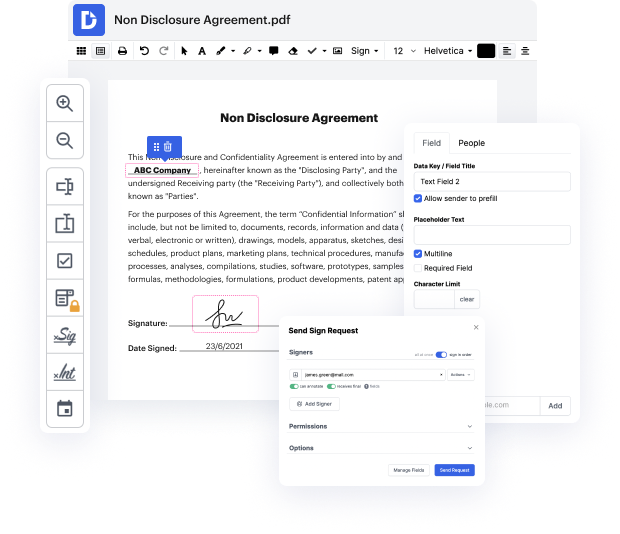
Many people find the process to inject evidence in xml rather challenging, particularly if they don't regularly deal with documents. However, today, you no longer have to suffer through long instructions or spend hours waiting for the editing app to install. DocHub lets you change documents on their web browser without setting up new applications. What's more, our robust service offers a full set of tools for professional document management, unlike numerous other online tools. That’s right. You no longer have to export and import your templates so often - you can do it all in one go!
Whatever type of paperwork you need to alter, the process is easy. Make the most of our professional online service with DocHub!
all right whatamp;#39;s up guys this is ryan from elevate security now in this video i wanted to go over exploiting one of what is perhaps one of the most commonly seen vulnerabilities across etfs especially oscp and things of that nature now iamp;#39;ve had the advantage of already at least attempting the oscp going through a lot of lab machines going through an exam and i will say without giving more information away than iamp;#39;m allowed to i will say as a very general statement that this vulnerability is one of the most common ones that i see and have to exploit so definitely one that i would say definitely will help you to learn if you have an interest in those things now the vulnerability that i am speaking of is the xml external entities injection or xxe exploit now iamp;#39;m going to be showcasing how to do that now before i do i want to mention that what can this vulnerability do for you right if youamp;#39;re able to exploit xxe you will get the ability to read any fi