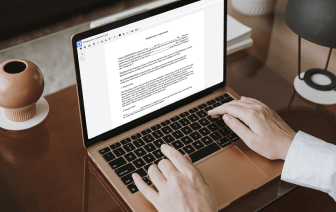
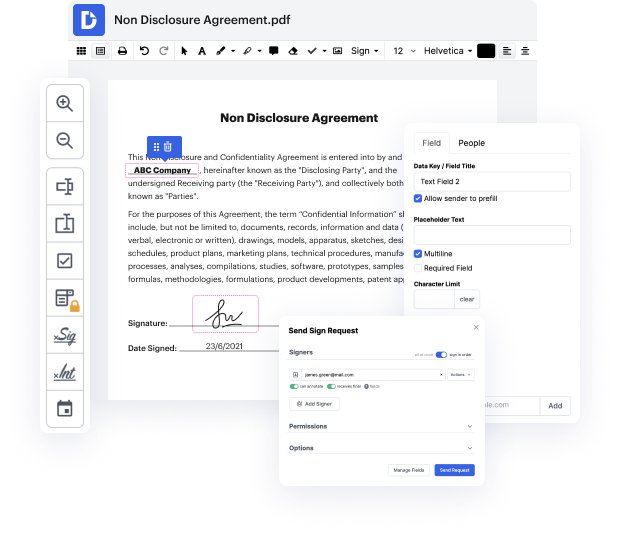
With DocHub, you can quickly inject email in LOG from any place. Enjoy features like drag and drop fields, editable text, images, and comments. You can collect eSignatures safely, add an additional level of defense with an Encrypted Folder, and work together with teammates in real-time through your DocHub account. Make changes to your LOG files online without downloading, scanning, printing or sending anything.
You can find your edited record in the Documents tab of your account. Prepare, send, print, or turn your file into a reusable template. Considering the variety of advanced features, it’s easy to enjoy smooth document editing and management with DocHub.
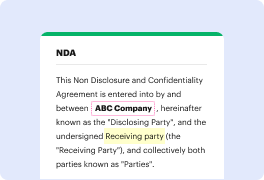
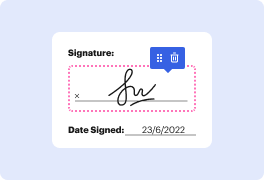
are you tired of juggling through multiple platforms and losing track of important customer emails well worry no more in todayamp;#39;s video weamp;#39;re going to show you a game changing feature that will revolutionize how you log emails in your CRM using the BCC or forwarding address so letamp;#39;s Dive Right In log into your HubSpot account and click on the settings icon in the main navigation bar in the left sidebar menu go to objects and click on activities then select the email login tab to the right of the BCC address field youamp;#39;ll find the BCC address provided by HubSpot click on the copy button to copy when composing a new email in your mail client at the BCC address to the BCE C line of the email ensures that the email contact will be automatically recorded on the contacts record in HubSpot for this you can click on contacts and locate the contact with the email address the email you sent will be logged in the contact activity area alternatively if youamp;#39;ve