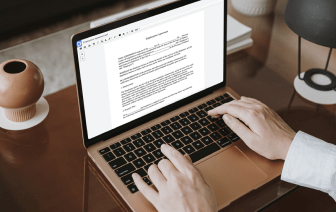
Flaws are present in every tool for editing every file type, and even though you can use many solutions out there, not all of them will suit your particular requirements. DocHub makes it easier than ever to make and alter, and deal with documents - and not just in PDF format.
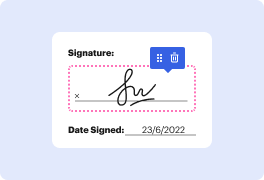
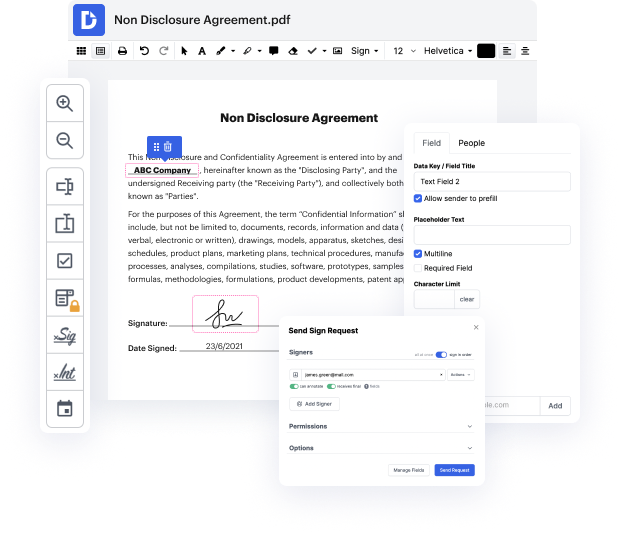
Every time you need to easily inject cross in html, DocHub has got you covered. You can quickly alter form elements including text and images, and structure. Customize, arrange, and encrypt documents, create eSignature workflows, make fillable forms for smooth information collection, etc. Our templates feature allows you to generate templates based on documents with which you frequently work.
Additionally, you can stay connected to your go-to productivity features and CRM solutions while handling your documents.
One of the most extraordinary things about leveraging DocHub is the option to deal with form activities of any difficulty, regardless of whether you require a fast tweak or more complex editing. It includes an all-in-one form editor, website document builder, and workflow-centered features. Additionally, you can be certain that your documents will be legally binding and comply with all security protocols.
Shave some time off your projects by leveraging DocHub's features that make handling documents easy.
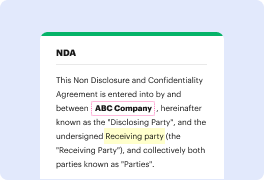
so the heading for this section is called exploit the vulnerable code using HTML injections so first thing letamp;#39;s log in as the root user and then itamp;#39;s provide the password thatamp;#39;s shown in lab 4 once inside of here weamp;#39;re going to navigate to your bank comm and then weamp;#39;re going to illustrate a couple of things one thing weamp;#39;re going to illustrate is how the PHP code that we inserted inside of our custom homepage how itamp;#39;s susceptible to HTML injections the other thing weamp;#39;re going to do is weamp;#39;re going to discuss what it means to be vulnerable to this type of attack so first thing letamp;#39;s right-click letamp;#39;s view the page source inside the page source weamp;#39;re going to scroll down and weamp;#39;re gonna find that name attribute inside of our input field and again this is what our request function our PHP request function how it was referencing the data that was supplied to the username input field was b