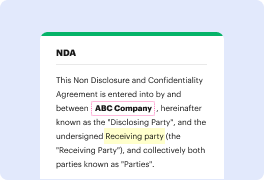
When you edit files in various formats day-to-day, the universality of your document tools matters a lot. If your instruments work for only a few of the popular formats, you might find yourself switching between application windows to inject company in html and handle other document formats. If you want to eliminate the hassle of document editing, get a platform that will easily manage any extension.
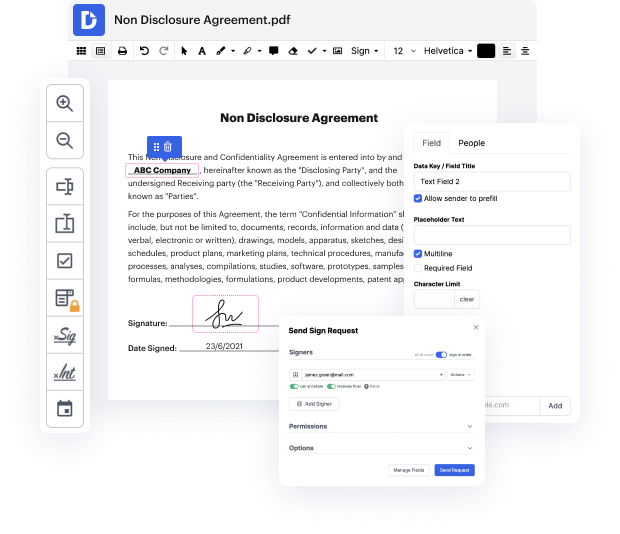
With DocHub, you do not need to concentrate on anything short of the actual document editing. You will not need to juggle programs to work with diverse formats. It will help you edit your html as easily as any other extension. Create html documents, modify, and share them in one online editing platform that saves you time and boosts your efficiency. All you need to do is sign up an account at DocHub, which takes only a few minutes.
You will not need to become an editing multitasker with DocHub. Its feature set is sufficient for fast papers editing, regardless of the format you need to revise. Begin with registering an account and discover how easy document management may be having a tool designed specifically to suit your needs.
hello everyone this is farming and welcome to cybersecurity TV in this video well be discussing about the HTML injection the basic concepts and at the end well also see the little demo on how to exploit the HTML injection with rabdi so lets get started in the previous video we discuss about the cross-site scripting so the HTML injection is similar to cross-site scripting in a sense that this is a client-side rendering attack so when the user input is not being sanitized and inserted into the application so for assume lets say the server or the client does not perform any sort of sanitization encoding decoding then the input provided by the user renders back to the page as is now just to put this in a perspective lets take a look at the demo so what I have done is I have prepared a simple HTML sorry PHP script in this one as you can see between the HTML and the body tail there is a welcome and we are getting the input from the user in the form of name name parameter and we are dis
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



