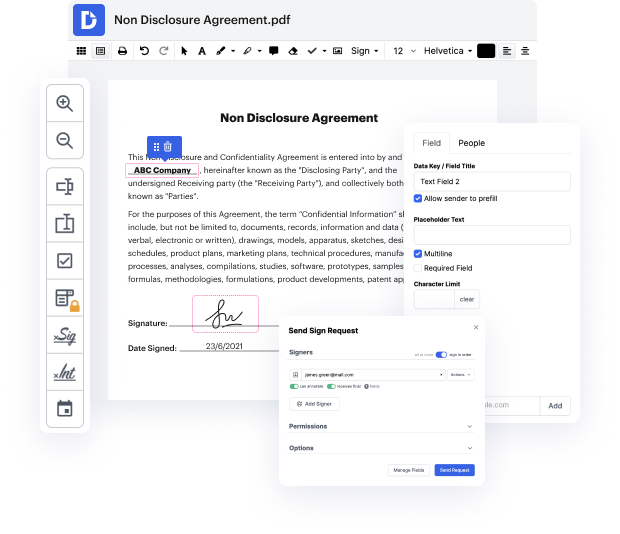
Needless to say, there’s no perfect software, but you can always get the one that perfectly combines robust functionality, intuitiveness, and reasonable cost. When it comes to online document management, DocHub provides such a solution! Suppose you need to Inject code in Security Agreement and manage paperwork efficiently and quickly. In that case, this is the appropriate editor for you - accomplish your document-related tasks anytime and from anywhere in only a few minutes.
Apart from rich functionality and straightforwardness, price is another great advantage of DocHub. It has flexible and cost-effective subscription plans and allows you to try our service for free over a 30-day trial. Try it out today!
hi again so today were going to look at how hackers on taking code on a web page i choose limited to an application called bewap its a intentionally made vulnerable application and the box i chose here is called php code injection and at the moment the security level is set to low basically this vulnerable application reflects a new junior developers project which is full of bugs so what happens if you connect jack code and well reflect code in certain way or inject code to a server how can you misuse that so lets assume that you want a page right now lets go ahead and go to the page php code injection were gonna hack it and we set the security current low and then here we see this is the page were gonna hack this now so this is just a test page reflecting back your message so im clicking this it says test im looking up in the get ul area on the browser this is test so if i wrote something like a hacker hello it would just write nothing it seems if i skipped the uh the space i
At DocHub, your data security is our priority. We follow HIPAA, SOC2, GDPR, and other standards, so you can work on your documents with confidence.
Learn more



